Choose the plan that meets your Security Requirements.
7 Days Money Back Guarantee. No questions asked.
Continuous WordPress Security Visibility
Aegisify Audit (WordPress & WebApp Security Scanner)
Find Real WordPress Security Risk Before It Turns Into Downtime, Data Loss, or Exposure.
From WordPress hardening and software-risk visibility to OWASP-aligned DAST, API discovery, and static code analysis, Aegisify Audit helps you see what is exposed, what changed, and what to fix next.
01.
Static Code SAST & Defensive Scans
Run internal WordPress security reviews for software risk, hardening posture, version exposure, and code quality across core, plugins, themes, users, and site drift.
02.
DAST Coverage extended Scans
Launch Quick DAST and Standard DAST to inspect public exposure, headers, login surface, REST routes, forms, browser surface, and other high-signal attack paths.
03.
Advanced Scans
Go deeper with Deep Auth DAST, API DAST, and Front-End DAST for authenticated workflow review, multi-role visibility, REST, GraphQL, OpenAPI discovery, and client-side exposure.
04.
Evidence, Reports & Remediation
Review findings with evidence, severity context, recent scan comparisons, downloadable CSV/PDF exports, and guided remediation workflows to move faster.
Offensive DAST Scans
Validate real web exposure with Quick DAST and Standard DAST. Covers OWASP-aligned public-facing checks, route and form discovery, REST surface visibility, browser-facing attack surface review, and high-signal testing for recurring security validation.
Static Scans
Best for internal WordPress assurance. Includes Vulnerability Scan, Standard Defensive Scan, and Static Code Analysis to review hygiene, software risk, hardening drift, and code-level issues. Static Code Analysis uses bundled PHPCS + WPCS analysis with Aegisify custom rules for deeper WordPress review.
Advanced Deep Scans
Use Deep Auth DAST, API DAST, and Front-End DAST for authenticated route inventory, authorization-focused review, REST/GraphQL/OpenAPI discovery, and front-end exposure analysis. Includes Compliance Baseline support for STIG/SRG-aligned posture checks in advanced workflows.
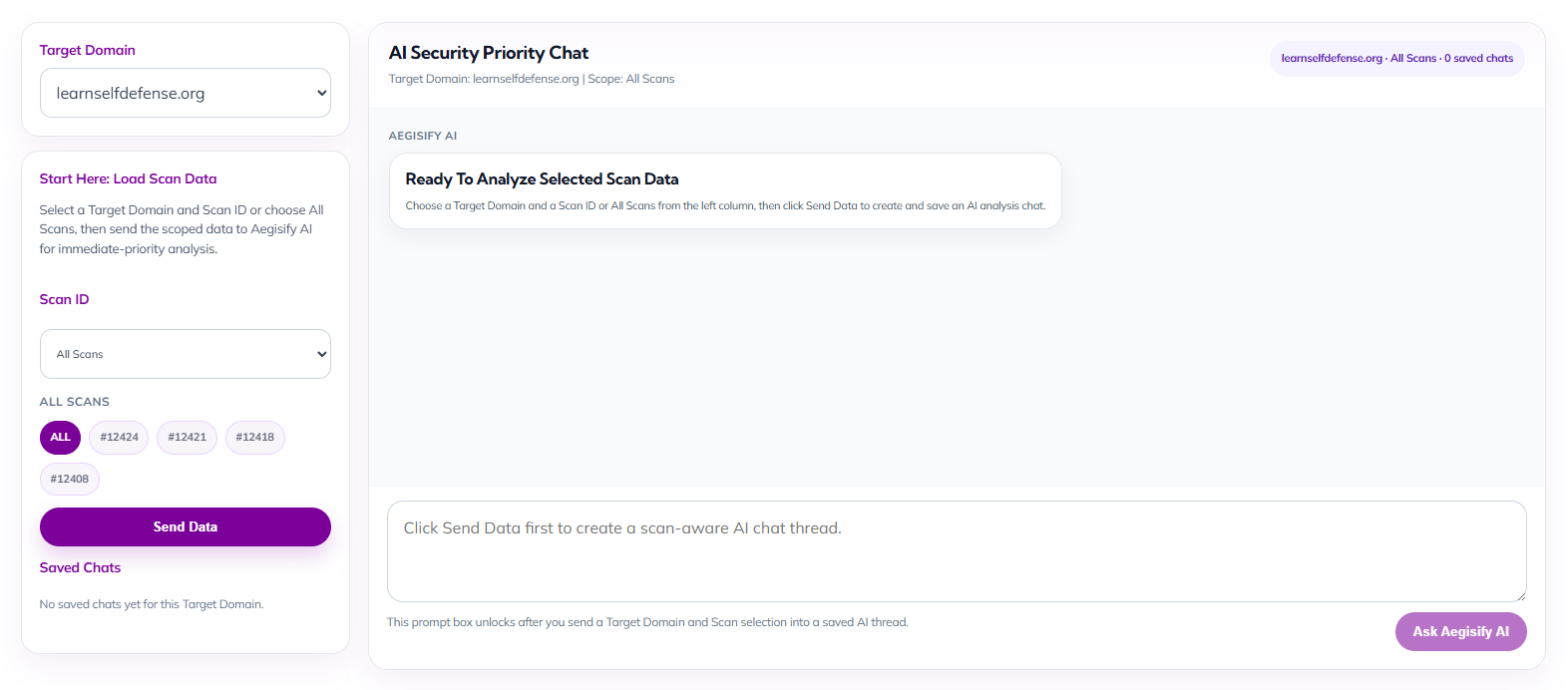
AI Security Priority Chat for Faster Decision-Making
Empower security executives and site owners with an AI-guided workspace built to turn scan data into immediate action. By selecting a target domain and scan scope, teams can launch a focused security conversation that helps prioritize risk, interpret findings faster, and streamline next-step decisions without digging through fragmented reports.
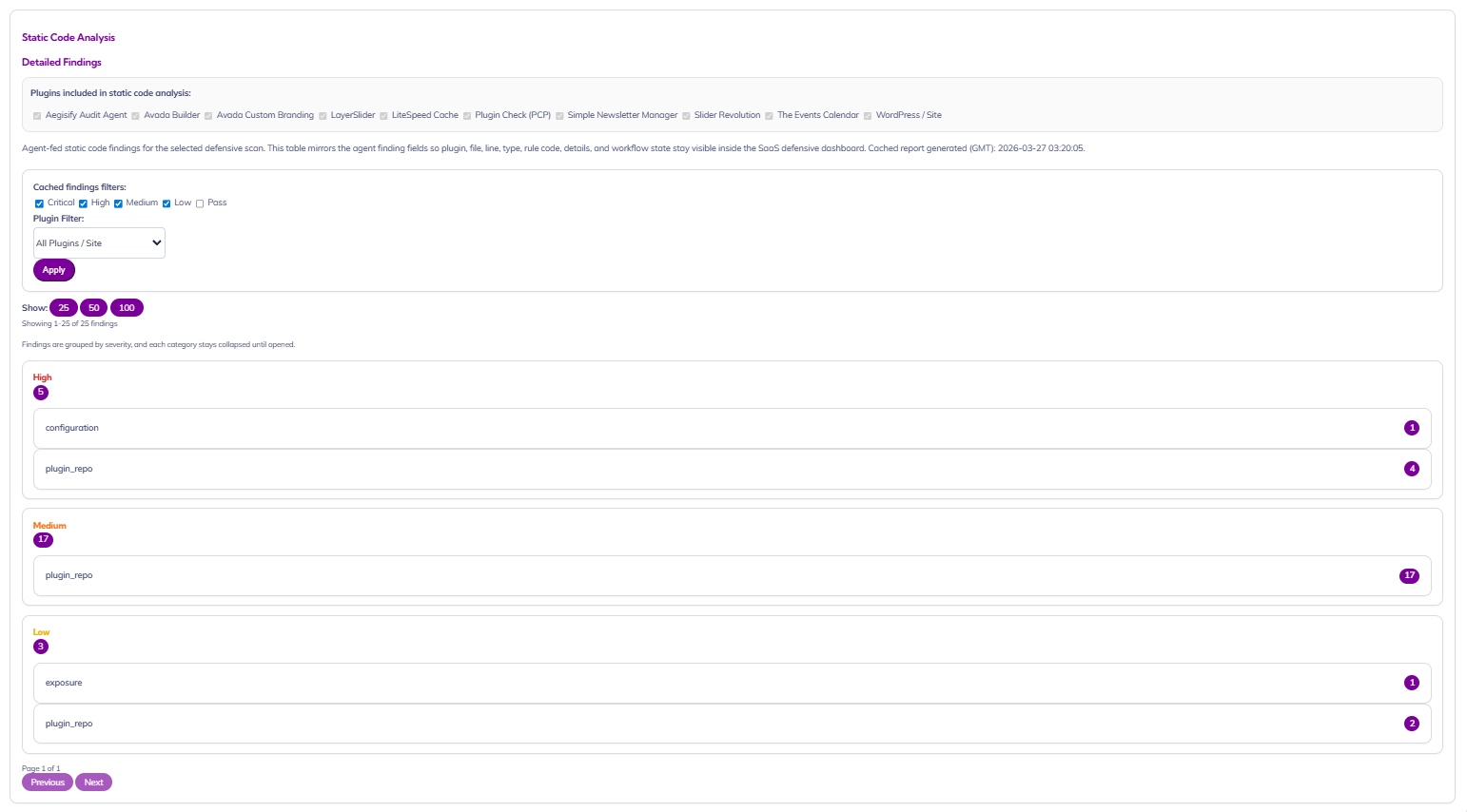
Static Code Analysis for WordPress Risk Visibility
Give security executives and site owners a clear view into code-level risk across the WordPress stack. This dashboard surfaces cached static analysis findings by plugin, file, severity, and rule category, making it easier to spot weak points in site components, prioritize remediation, and maintain a stronger security posture without digging through raw technical output.
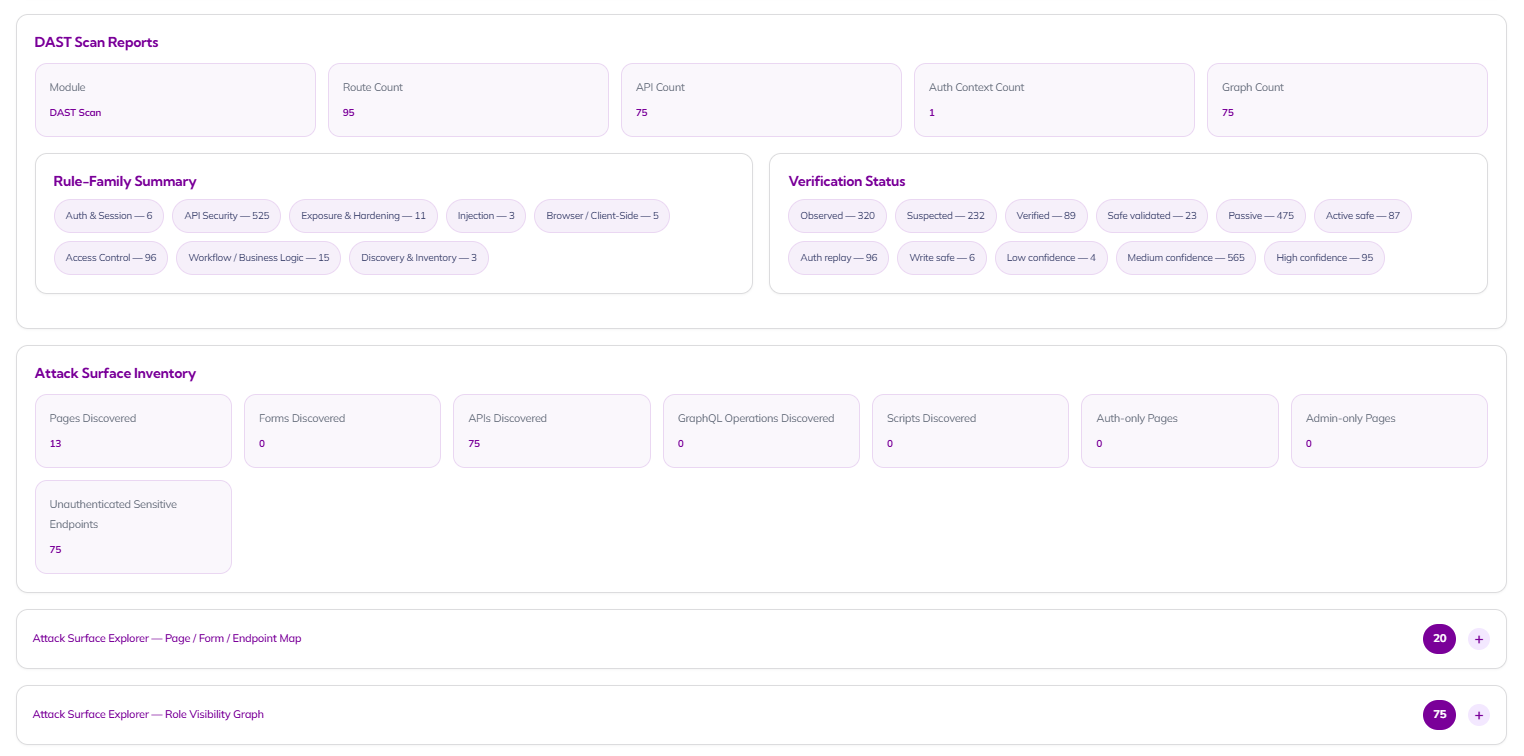
DAST Scan Reports / Attack Surface Inventory
Give security leaders and site owners an instant, board-ready view of live application exposure. This dashboard turns complex scan data into clear operational insight by showing route coverage, API footprint, auth-context visibility, verification status, and attack surface inventory in one place so teams can quickly understand where risk exists and where validation is still needed.
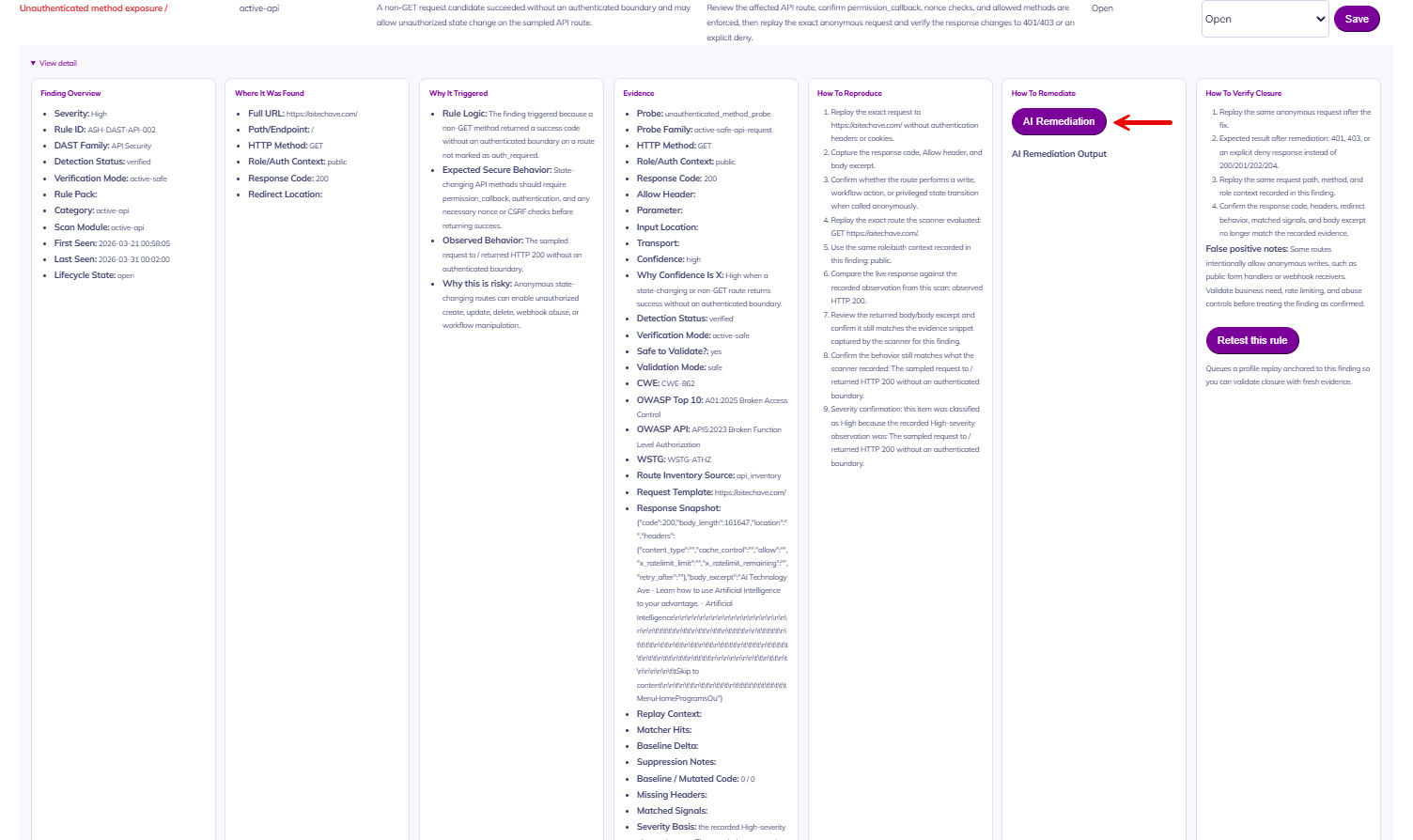
From Detection to Remediation in One Workflow
Move beyond raw findings and into real response. This detailed finding view gives executives and operators the full story behind every issue: severity, rule ID, evidence, trigger logic, reproduction steps, remediation guidance, and validation instructions while built-in AI remediation instructions helps teams accelerate closure without losing context.
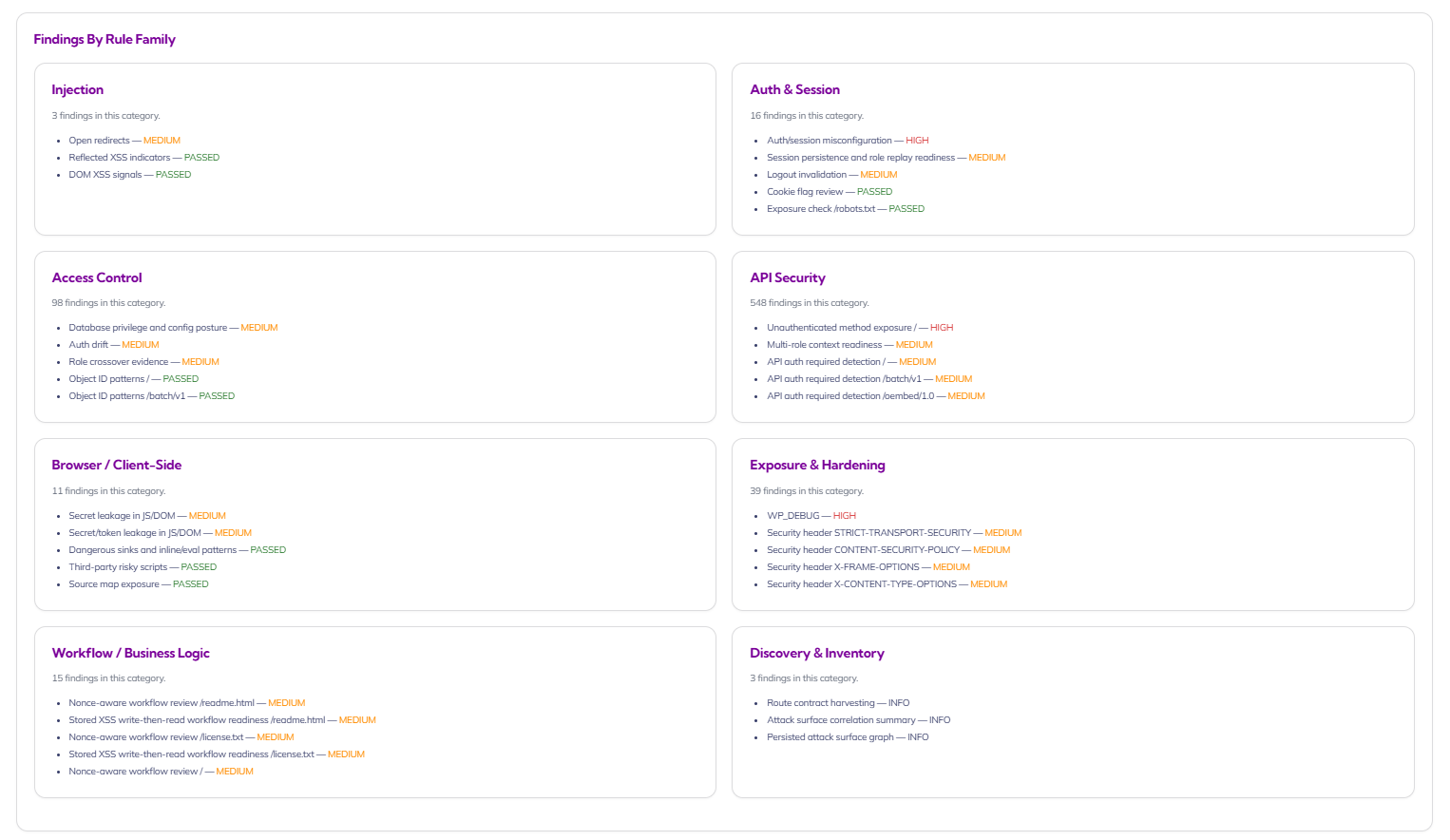
Risk Organized by Rule Family, Not Noise
Turn overwhelming scan output into structured, decision-ready intelligence. By organizing findings into rule families like Injection, Auth & Session, Access Control, API Security, Browser/Client-Side, Exposure & Hardening, Workflow/Business Logic, and Discovery & Inventory, this view helps security teams prioritize systemic weaknesses while giving site owners a clearer picture of where their application posture needs attention.
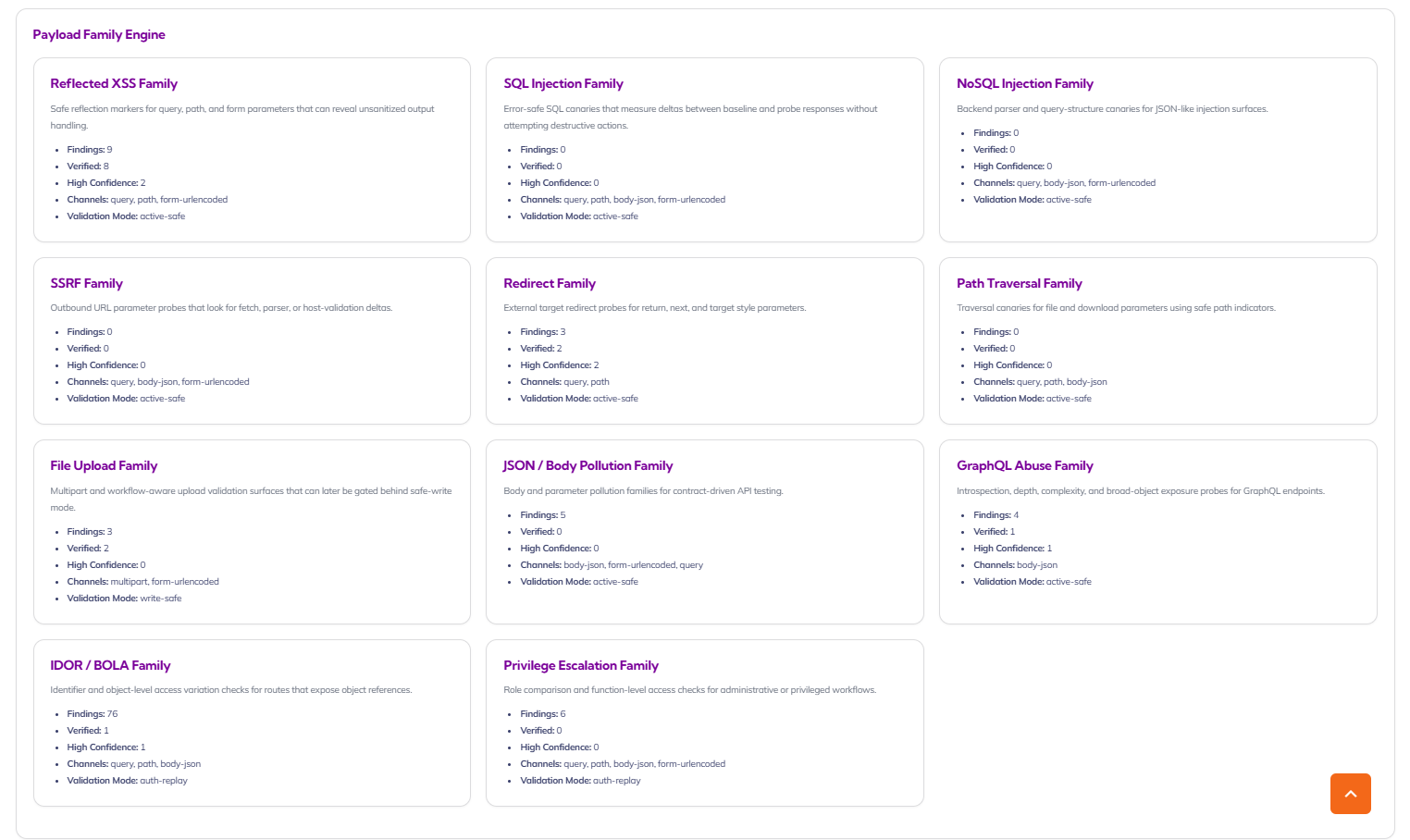
Payload Family Engine for Real-World Attack Simulation
See how your application stands up against the attack patterns that matter most. The Payload Family Engine organizes results by offensive test family such as XSS, SSRF, file upload, JSON/body pollution, GraphQL abuse, IDOR/BOLA, and privilege escalation giving security teams a clearer way to understand coverage, validation mode, and the concentration of risk across modern web applications and APIs.
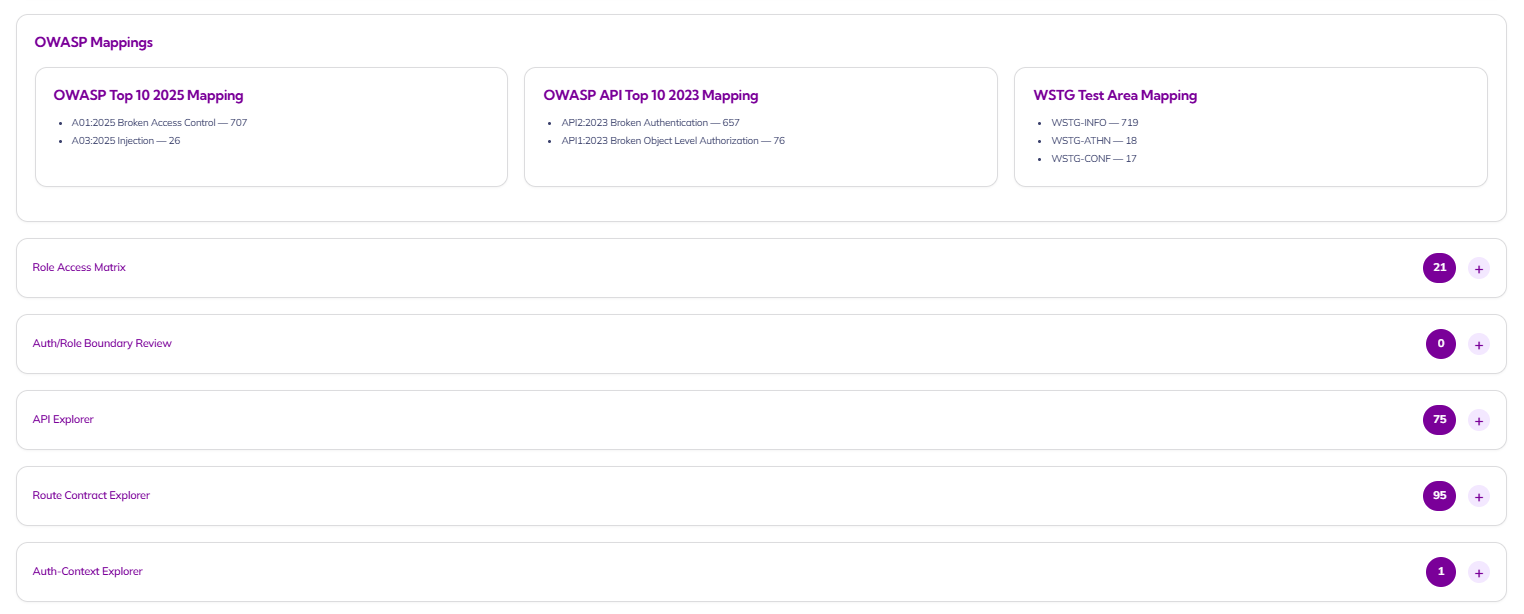
OWASP-Aligned Reporting with Explorable Security Context
Translate technical findings into recognized security frameworks your leadership team already understands. This view maps results to OWASP Top 10, OWASP API Top 10, and WSTG test areas while also exposing role access matrices, API exploration, route contracts, and auth-context insight helping security executives communicate risk clearly and helping site owners understand where protection needs to improve.
Building the Future of Security
Public artifact and exposure checks
Aegisify Free Test performs 59 external website security checks and delivers a clear findings report covering transport security, exposure risk, API discovery, OWASP-style attack indicators, and login/session surface review.

