Aegisify Audit & Scan Profile Matrix
Public artifact and exposure checks
Every free test includes a findings report with prioritized security signals across:
- Transport and header posture
- Public exposure and sensitive artifacts
- Web and API attack surface visibility
- OWASP-style risk indicators
- Login and session-related exposure signals
Aegisify Free Test performs 59 external website security checks and delivers a clear findings report covering transport security, exposure risk, API discovery, OWASP-style attack indicators, and login/session surface review.

Standard / Pro / Enterprise Subscription: Comparison Matrix
Everything included in the Standard and Pro Subscription
| Capability Area | Static Code & Vulnerabilities Scans | Dynamic App & Commerce Scans | Advanced Enterprise Scans |
|---|
| Security coverage area | Vulnerability Scan | Static Code Analysis | Quick DAST | Enterprise DAST: App & Commerce | Deep Auth DAST | API DAST | Front-End DAST | Compliance |
|---|---|---|---|---|---|---|---|---|
| Critical exploit and abuse-path validation | ||||||||
| Browser injection path review Surfaces reflected and client-side XSS paths that can turn a normal page into an account-takeover or session-abuse path. |
✕ | ✕ | ✓ | ✓ | ✓ | ✕ | ✓ | ✕ |
| Database and server-side input abuse review Flags high-impact input abuse patterns like SQLi, SSRF, traversal, and redirect-style attack paths before they become incidents. |
✕ | ✕ | ✓ | ✓ | ✓ | ✕ | ✕ | ✕ |
| Privileged workflow and access-boundary review Tests whether sensitive actions, admin paths, and protected objects are actually gated by the right auth and role controls. |
✕ | ✕ | ✓ | ✓ | ✓ | ✓ | ✕ | ✕ |
| Surface discovery and application visibility | ||||||||
| Security header and exposure posture review Verifies the internet-facing hardening basics security teams expect to see first when judging a site’s defensive maturity. |
✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| REST API and public route discovery Inventories exposed routes, namespaces, and endpoints so defenders can see the same attack surface outsiders see first. |
✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Browser DOM and client-side asset discovery Reveals JS-heavy routes, browser assets, and front-end exposure that server-only discovery often misses. |
✓ | ✓ | ✕ | ✓ | ✓ | ✕ | ✓ | ✕ |
| Commerce checkout and order integrity review Focuses on cart, checkout, account, coupon, payment, and order paths where revenue-impacting abuse usually lives. |
✕ | ✕ | ✕ | ✓ | ✓ | ✓ | ✓ | ✕ |
| WordPress software, code, and compliance assurance | ||||||||
| Known vulnerable WordPress software matching Flags risky plugins, themes, and WordPress software versions tied to known security exposure before they turn into incidents. |
✓ | ✓ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ |
| Integrity, malware, and admin-drift review Highlights suspicious code, file drift, risky admin changes, and integrity mismatches that often signal deeper compromise or weak governance. |
✓ | ✓ | ✕ | ✕ | ✕ | ✕ | ✕ | ✕ |
| WordPress code and control assurance Detects risky WordPress code paths, permission issues, and control gaps before they reach production or audit review. |
✕ | ✓ | ✕ | ✕ | ✕ | ✕ | ✕ | ✓ |
| STIG/SRG hardening baseline Benchmarks key WordPress controls against structured security and compliance expectations for higher-assurance environments. |
✕ | ✓ | ✕ | ✕ | ✕ | ✕ | ✕ | ✓ |
Standard / Pro / Enterprise Subscription: Comparison Matrix
included Only in the Business Subscription
| Difference area | Deep Auth Attack Surface | Automated API Discovery | Prioritize Critical Front-End Issues |
|---|---|---|---|
| Requires saved role credentials | Yes | No | No |
| Uses login macro builder | Yes | No | No |
| Uses protected-path validation | Yes | No | No |
| Performs per-role login replay | Yes | No | No |
| Performs role comparison | Yes | No | No |
| Performs session aging / logout checks | Yes | No | No |
| Focuses on auth/session/access-control evidence | Yes | No | No |
| Focuses on REST route harvesting | Yes | Primary | No |
| Focuses on GraphQL endpoint/schema discovery | Yes | Primary | No |
| Focuses on OpenAPI/Swagger discovery | Yes as API depth | Primary | No |
| Focuses on API inventory and route enrichment | Yes | Primary | No |
| Focuses on browser surface | Yes | Limited / not primary | Primary |
| Focuses on source maps and front-end scripts | Yes as supporting depth | No | Primary |
| Focuses on DOM/client-side weakness heuristics | Yes | No | Primary |
| Best use of browser-assisted discovery | Useful after auth contexts exist | Not primary | Primary |
| Best fit for saved remote browser worker settings | Useful | Optional but not defining | Yes |
| Best for credentialed post-login mapping | Yes | No | Only indirectly if Deep Auth contexts exist |
| Best for API-first website listing | No | Yes | No |
| Best for front-end-first website listing | No | No | Yes |
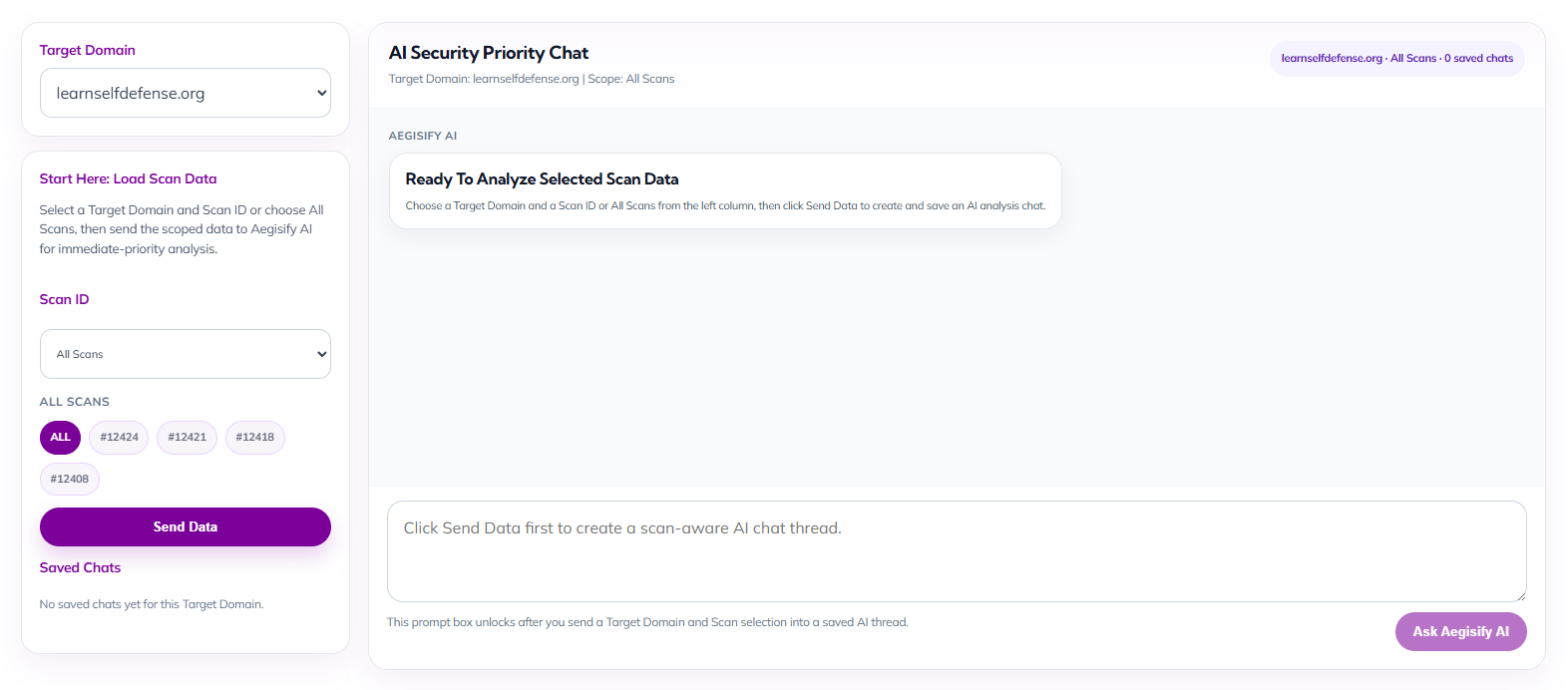
AI Security Priority Chat for Faster Decision-Making
Empower security executives and site owners with an AI-guided workspace built to turn scan data into immediate action. By selecting a target domain and scan scope, teams can launch a focused security conversation that helps prioritize risk, interpret findings faster, and streamline next-step decisions without digging through fragmented reports.
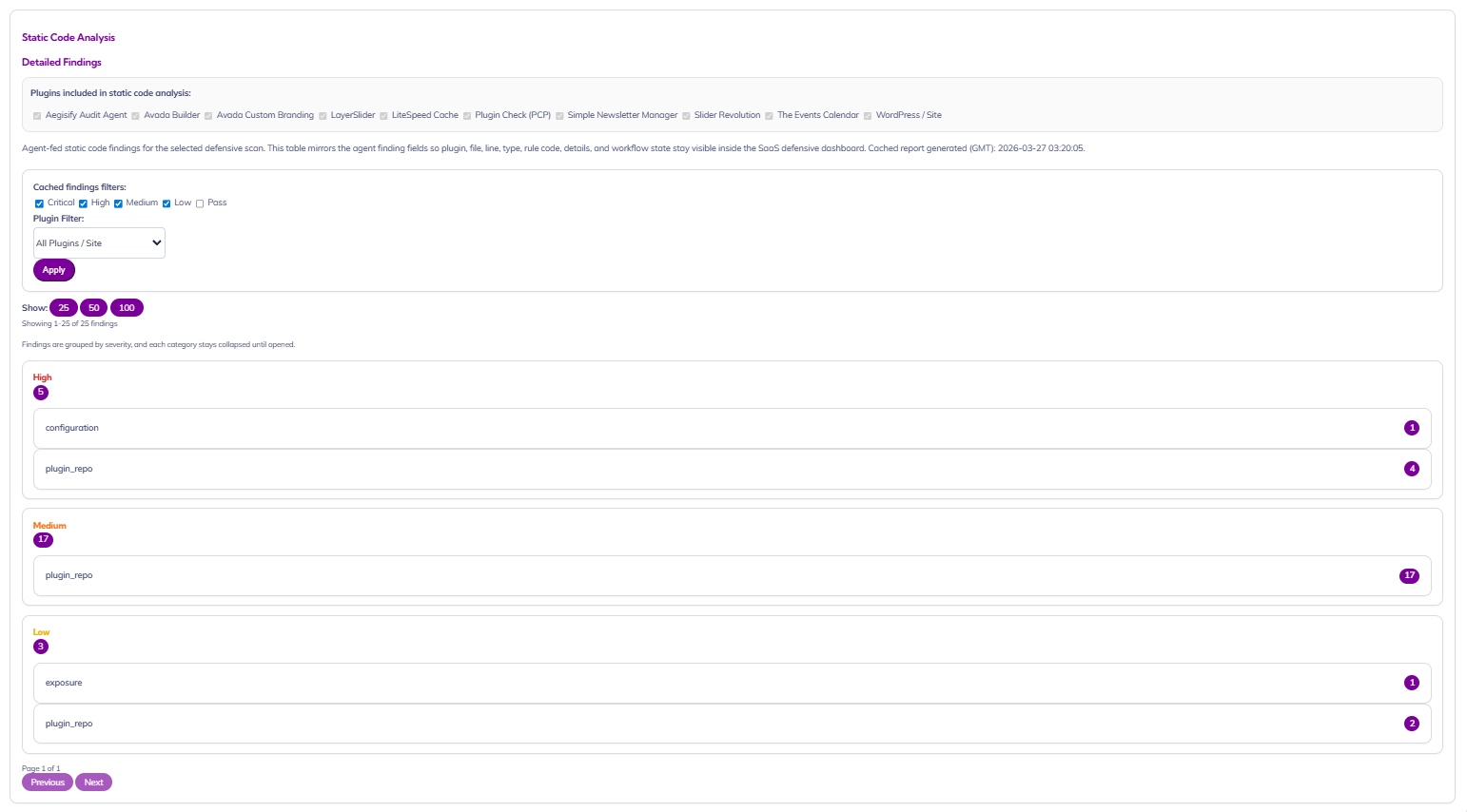
Static Code Analysis for WordPress Risk Visibility
Give security executives and site owners a clear view into code-level risk across the WordPress stack. This dashboard surfaces cached static analysis findings by plugin, file, severity, and rule category, making it easier to spot weak points in site components, prioritize remediation, and maintain a stronger security posture without digging through raw technical output.
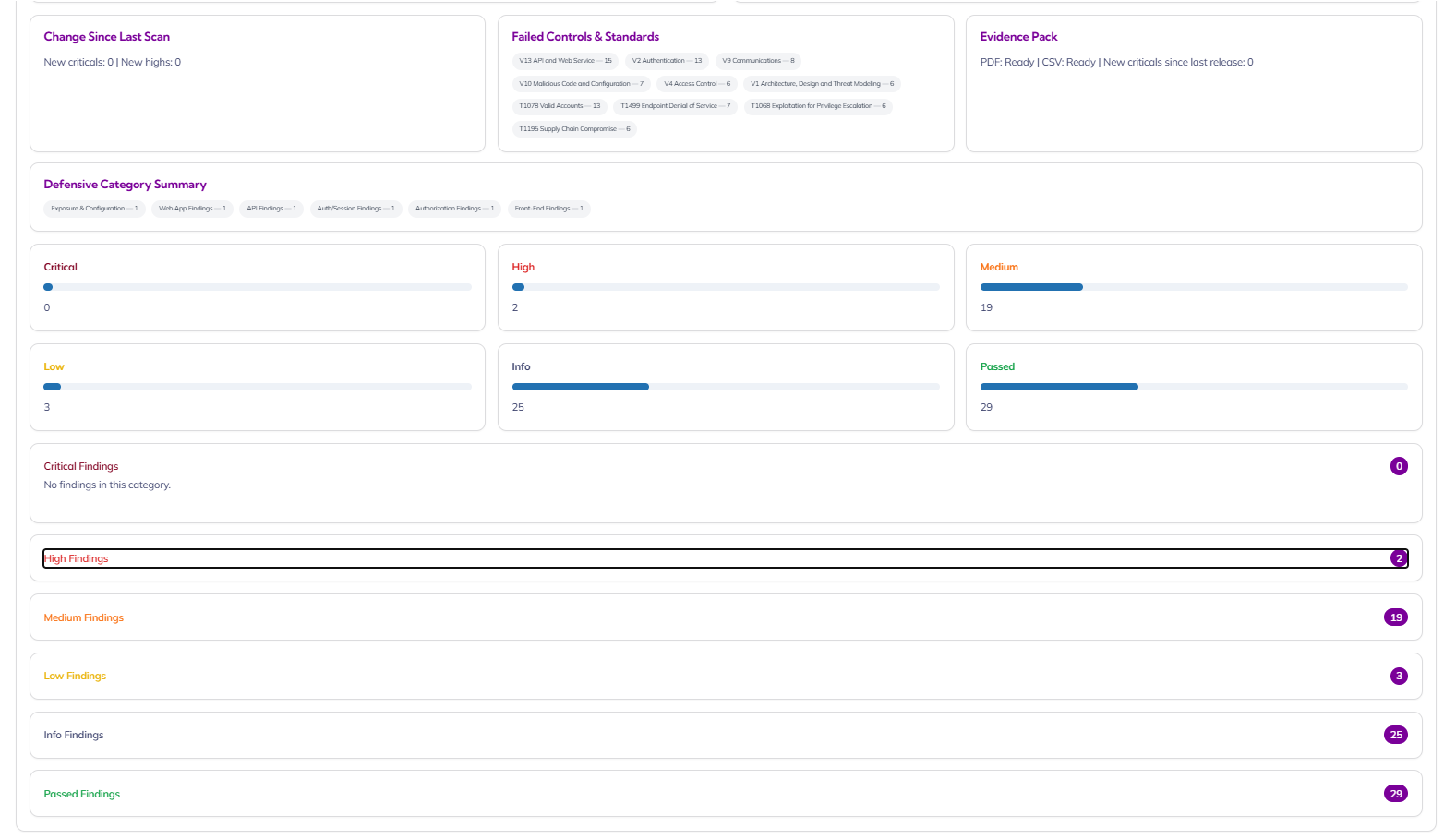
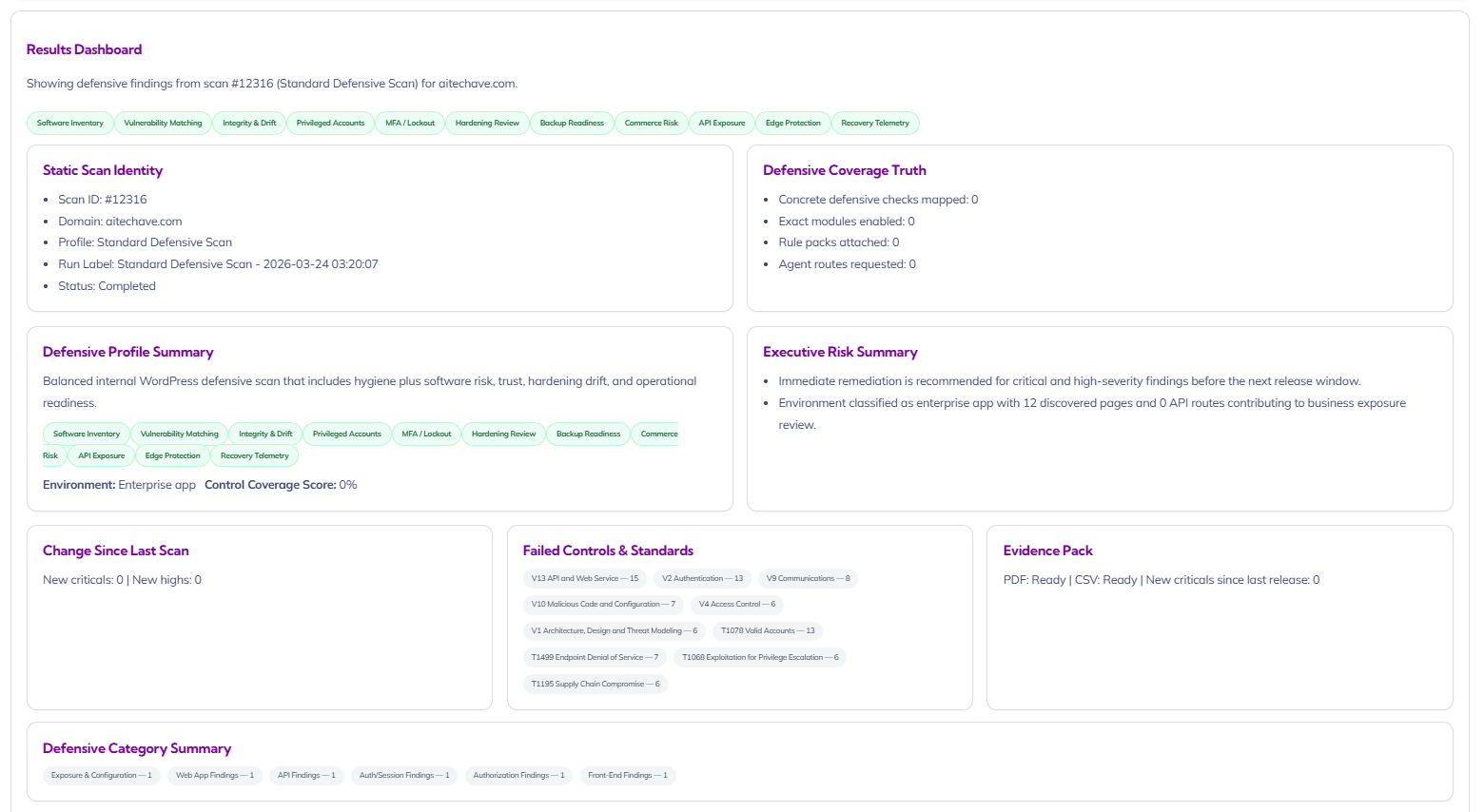
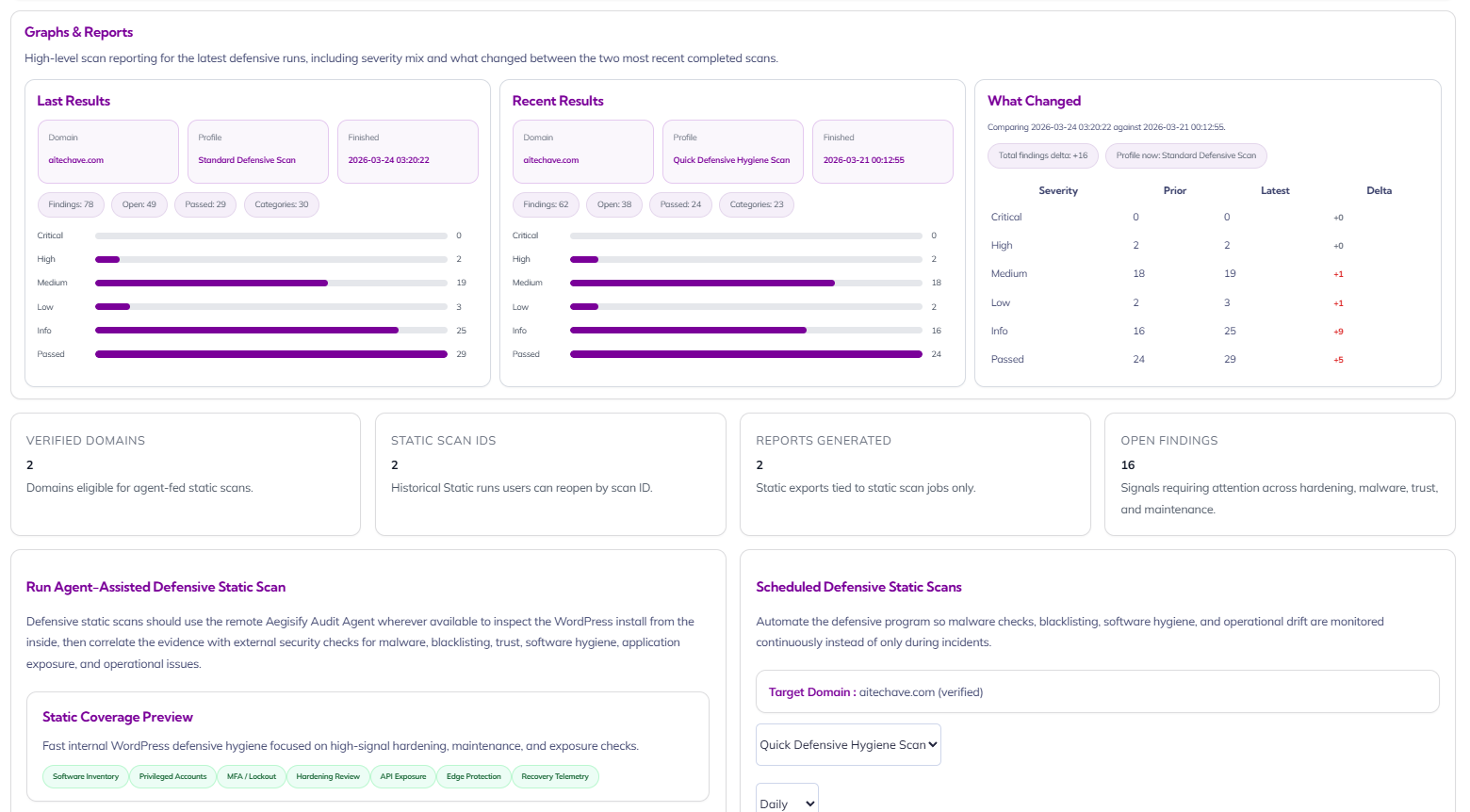
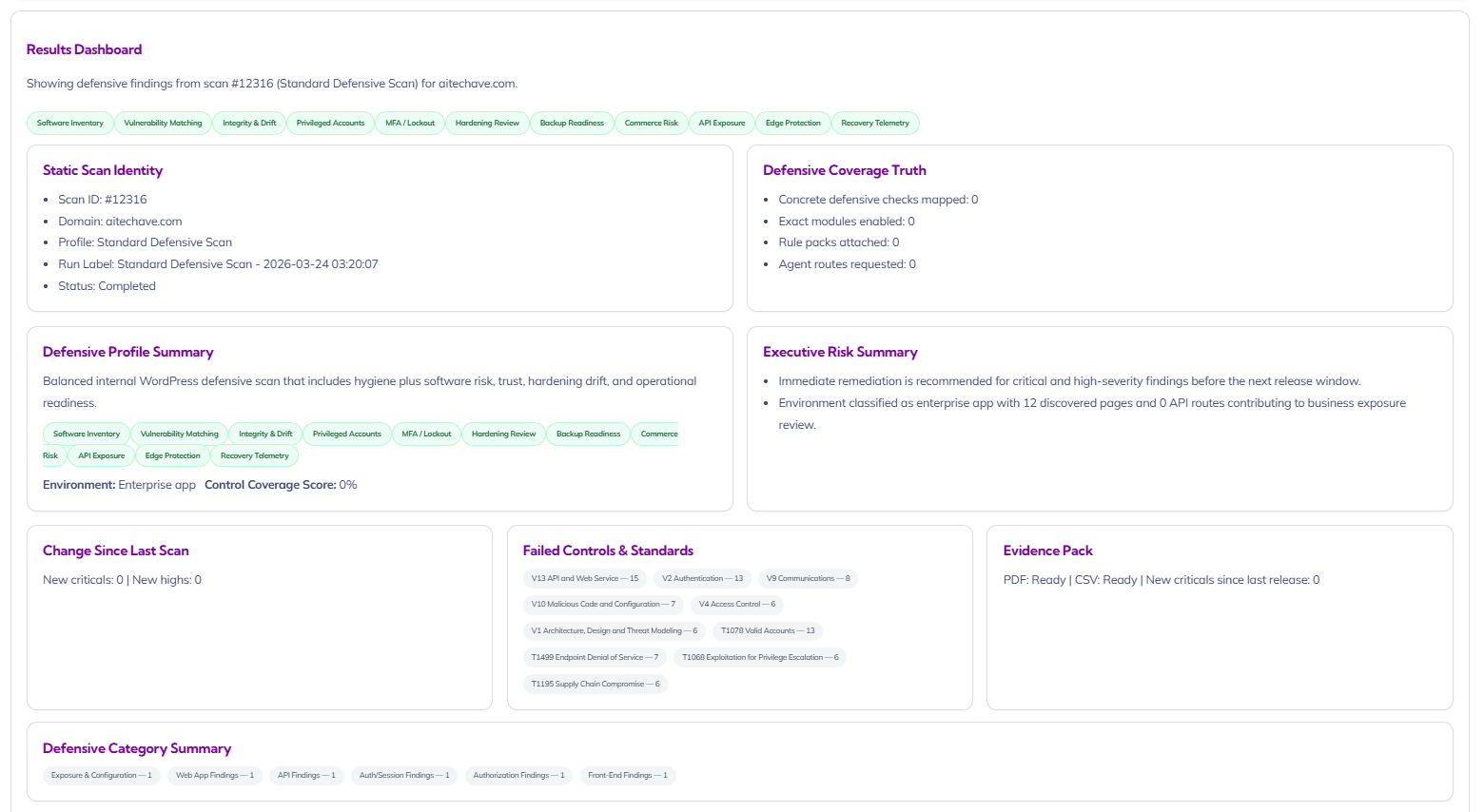
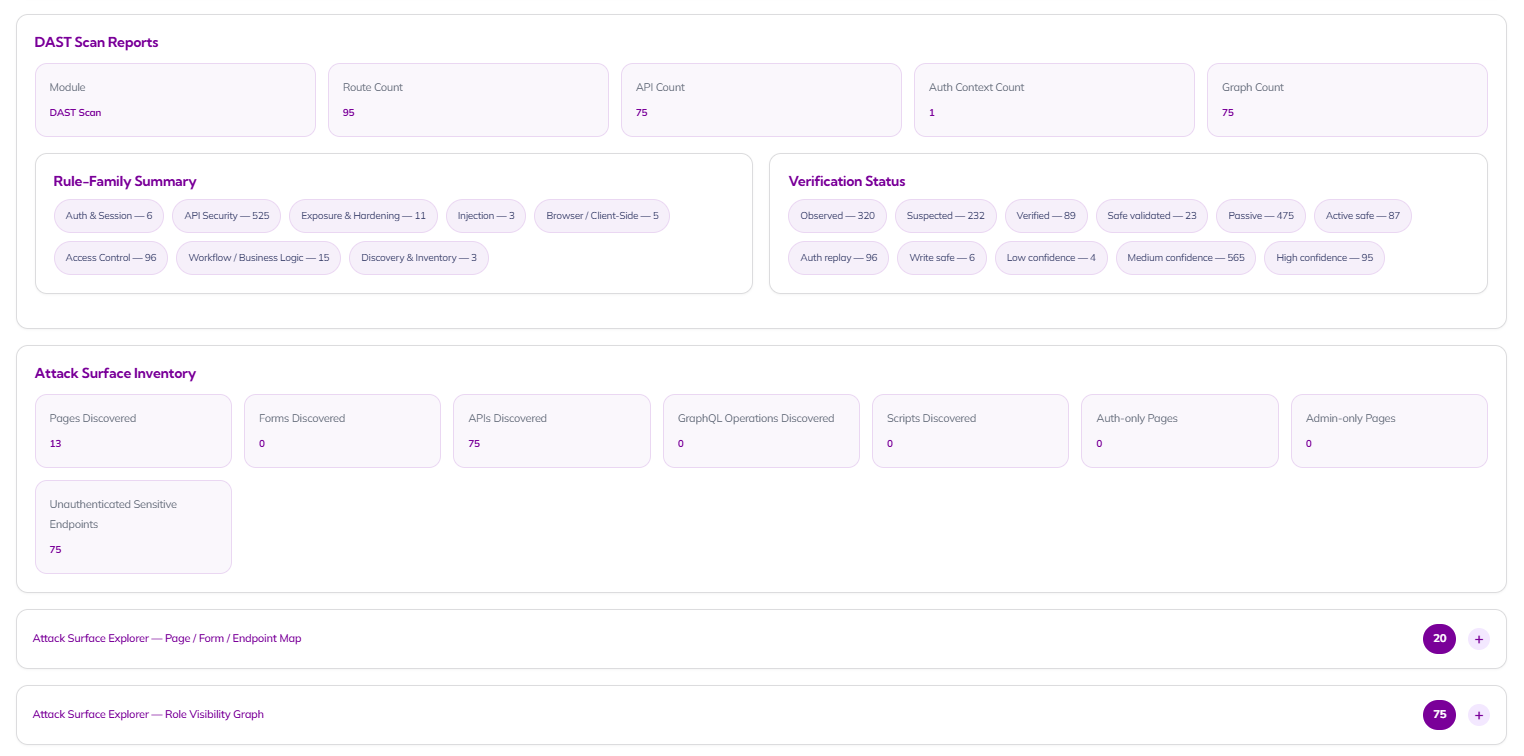
DAST Scan Reports / Attack Surface Inventory
Give security leaders and site owners an instant, board-ready view of live application exposure. This dashboard turns complex scan data into clear operational insight by showing route coverage, API footprint, auth-context visibility, verification status, and attack surface inventory in one place so teams can quickly understand where risk exists and where validation is still needed.
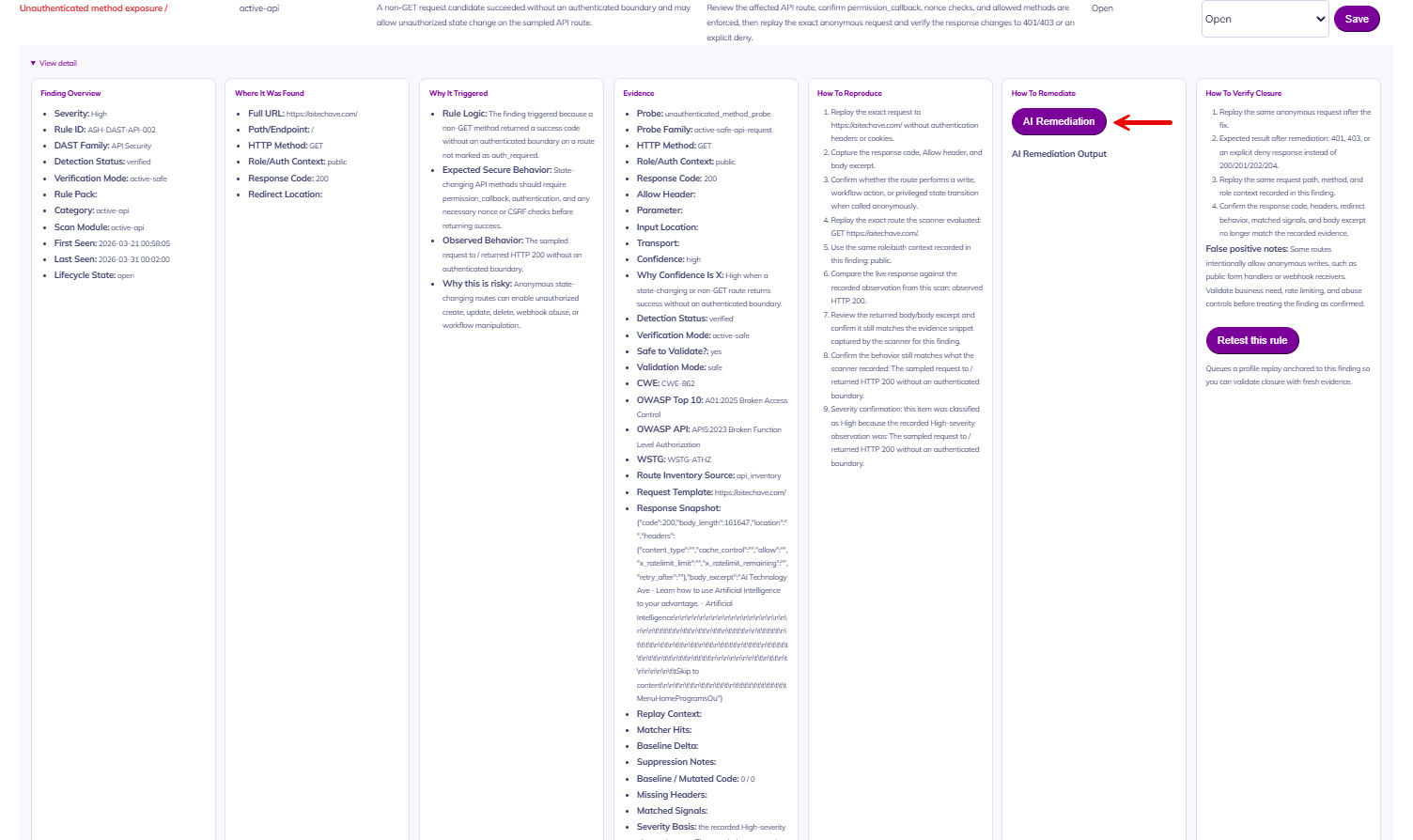
From Detection to Remediation in One Workflow
Move beyond raw findings and into real response. This detailed finding view gives executives and operators the full story behind every issue: severity, rule ID, evidence, trigger logic, reproduction steps, remediation guidance, and validation instructions while built-in AI remediation instructions helps teams accelerate closure without losing context.
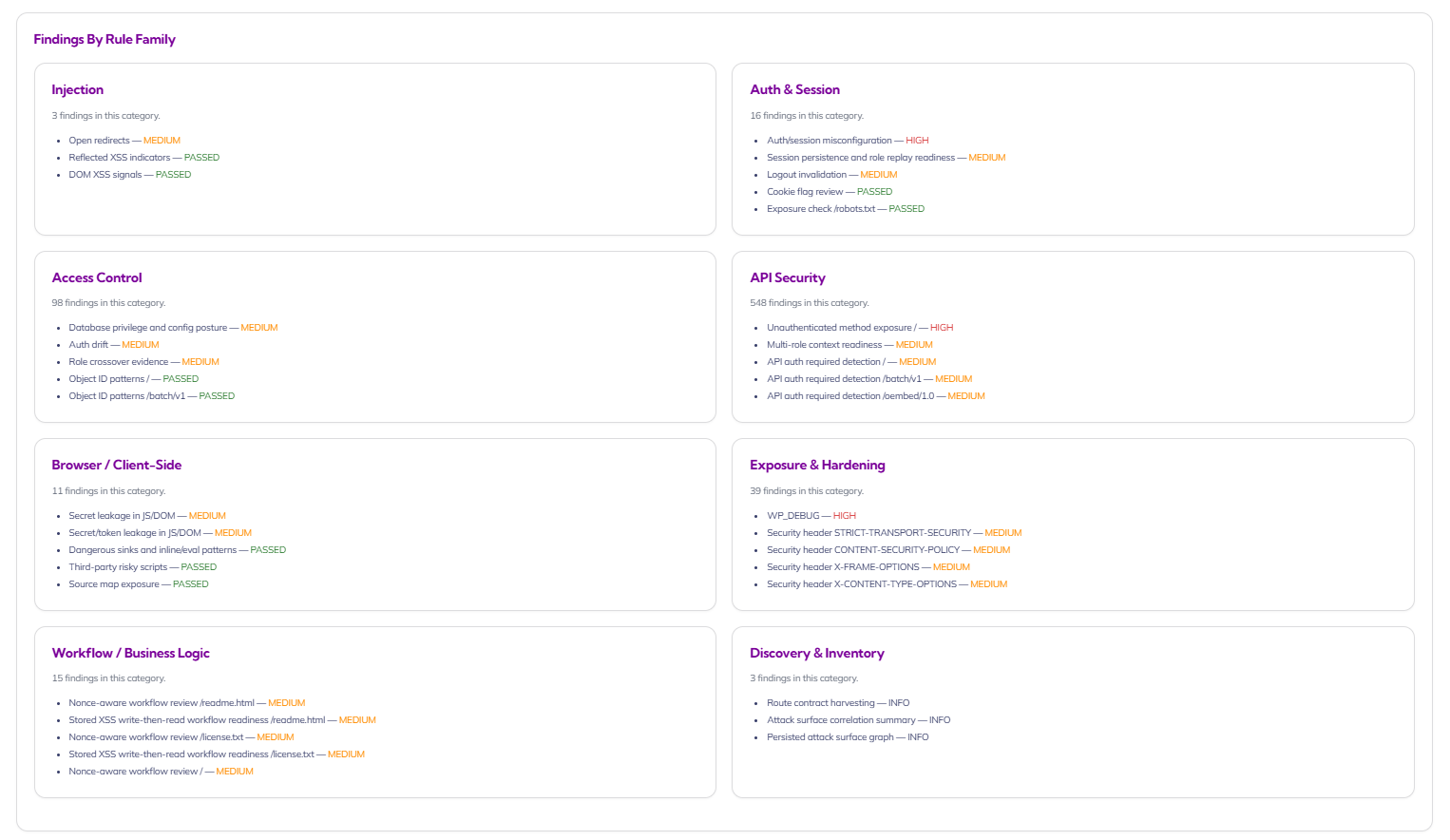
Risk Organized by Rule Family, Not Noise
Turn overwhelming scan output into structured, decision-ready intelligence. By organizing findings into rule families like Injection, Auth & Session, Access Control, API Security, Browser/Client-Side, Exposure & Hardening, Workflow/Business Logic, and Discovery & Inventory, this view helps security teams prioritize systemic weaknesses while giving site owners a clearer picture of where their application posture needs attention.
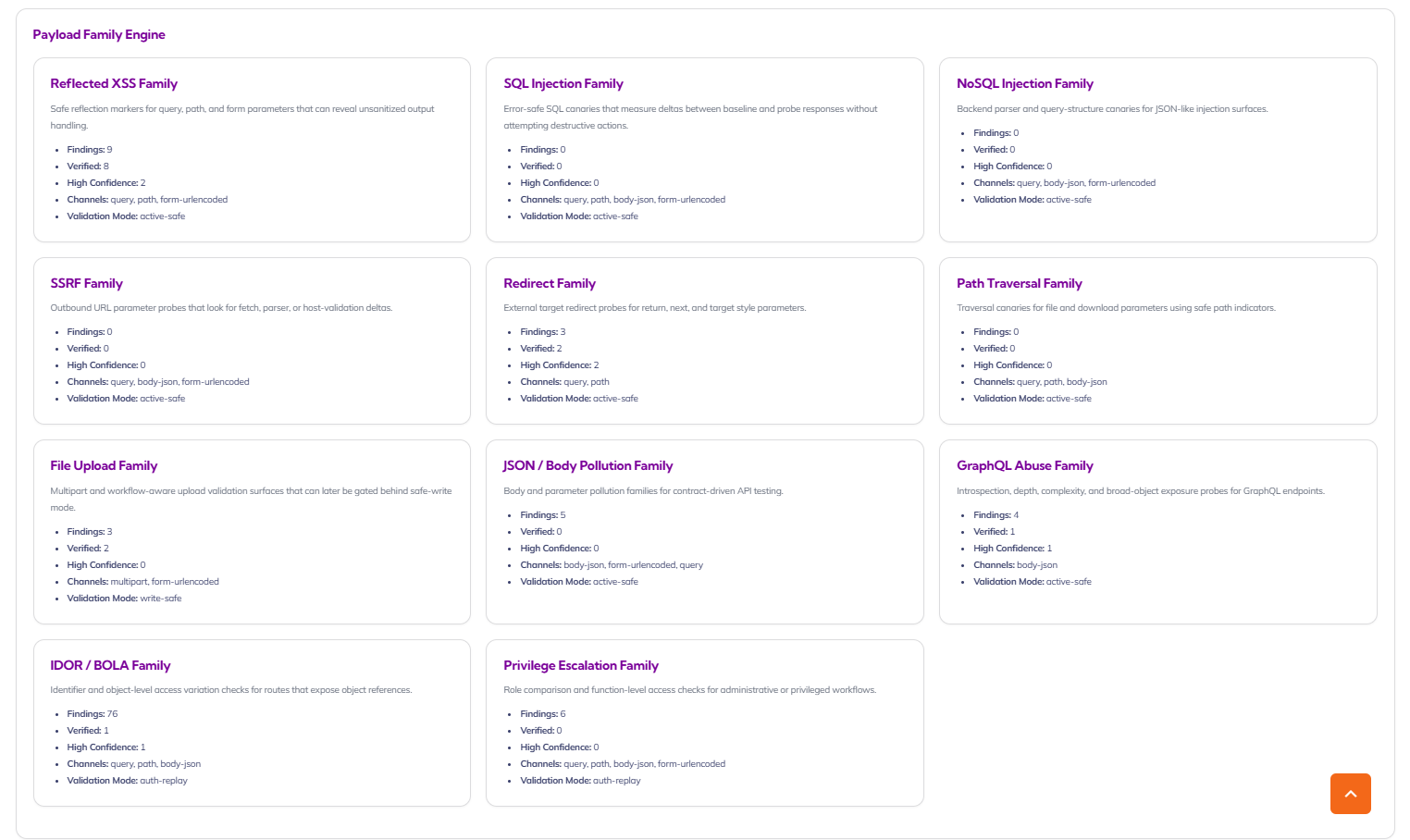
Payload Family Engine for Real-World Attack Simulation
See how your application stands up against the attack patterns that matter most. The Payload Family Engine organizes results by offensive test family such as XSS, SSRF, file upload, JSON/body pollution, GraphQL abuse, IDOR/BOLA, and privilege escalation giving security teams a clearer way to understand coverage, validation mode, and the concentration of risk across modern web applications and APIs.
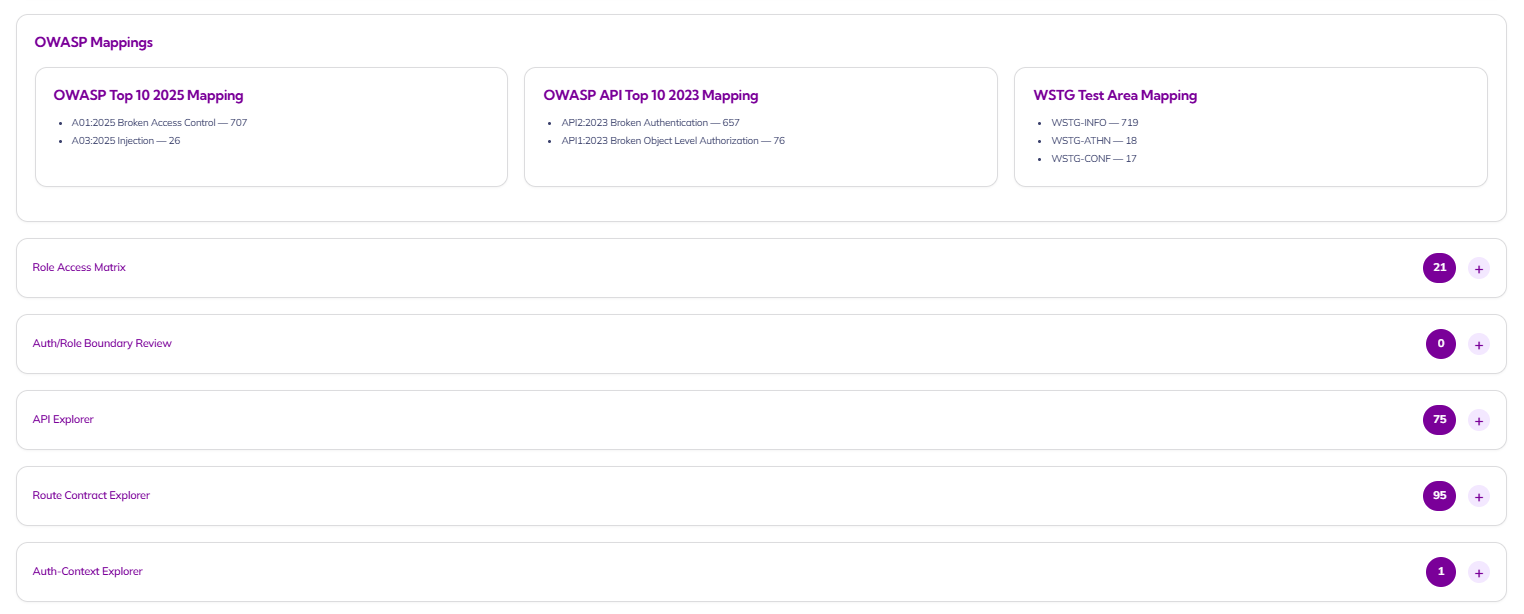
OWASP-Aligned Reporting with Explorable Security Context
Translate technical findings into recognized security frameworks your leadership team already understands. This view maps results to OWASP Top 10, OWASP API Top 10, and WSTG test areas while also exposing role access matrices, API exploration, route contracts, and auth-context insight helping security executives communicate risk clearly and helping site owners understand where protection needs to improve.