The value of a WordPress security scanner is not only detection. The value is turning detection into prioritization, evidence, action, and measurement.
A WordPress security scanner should not function like a smoke alarm that keeps beeping without context. Professional teams need to know which alerts are urgent, which are informational, which require developer review, which require a WAF or host-level control, and which could affect revenue, uptime, compliance posture, or search visibility.
What a Professional WordPress Security Scanner Should Do
A mature scanner should help answer these questions:
- Are WordPress core, plugins, and themes exposed to known vulnerabilities?
- Are there malware indicators, backdoors, SEO spam signals, malicious redirects, or blacklist status concerns?
- Are sensitive files, logs, backup artifacts, debug traces, or configuration clues publicly exposed?
- Are security headers, cookies, login behavior, APIs, and routes aligned with expected hardening practices?
- Can engineering and leadership review a clear report instead of disconnected plugin notices?
- Can the organization monitor risk over time with alerts, reports, and scan history?
Aegisify Security Scanner Coverage
Vulnerability Scanner Coverage
Aegisify helps review plugin vulnerabilities, theme vulnerabilities, core vulnerabilities, CVEs, fixed versions, dependency risk, and component inventory. This is the foundation of WordPress security because attackers frequently target known weaknesses in widely deployed plugins and themes.
Malware Scanner Signals
Malware risk is not limited to obvious malicious files. Professional review should consider backdoors, suspicious file changes, SEO spam, malicious redirects, blacklist status, reputation signals, debug logs, and unexpected behavior. Aegisify should be positioned as helping detect indicators and guide cleanup review, not as guaranteeing complete automated removal.
Public Exposure and DAST-Style Review
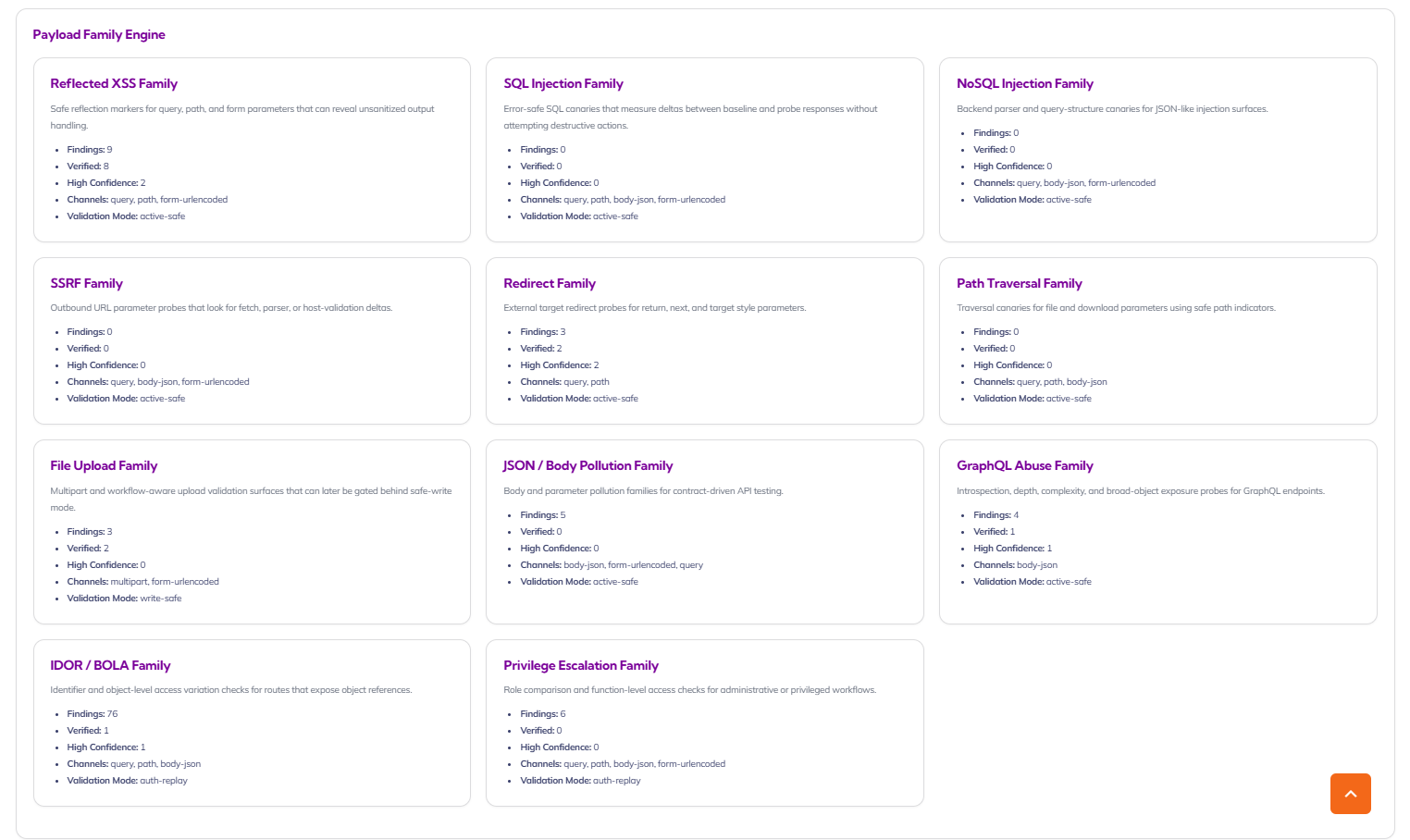
Aegisify offensive scan workflows can support DAST-style review of web-facing behavior. That includes headers, cookies, login surfaces, public WordPress artifacts, API inventory, OpenAPI hints, GraphQL hints, and payload family coverage such as SQL injection, NoSQL injection, SSRF, and path traversal candidates.
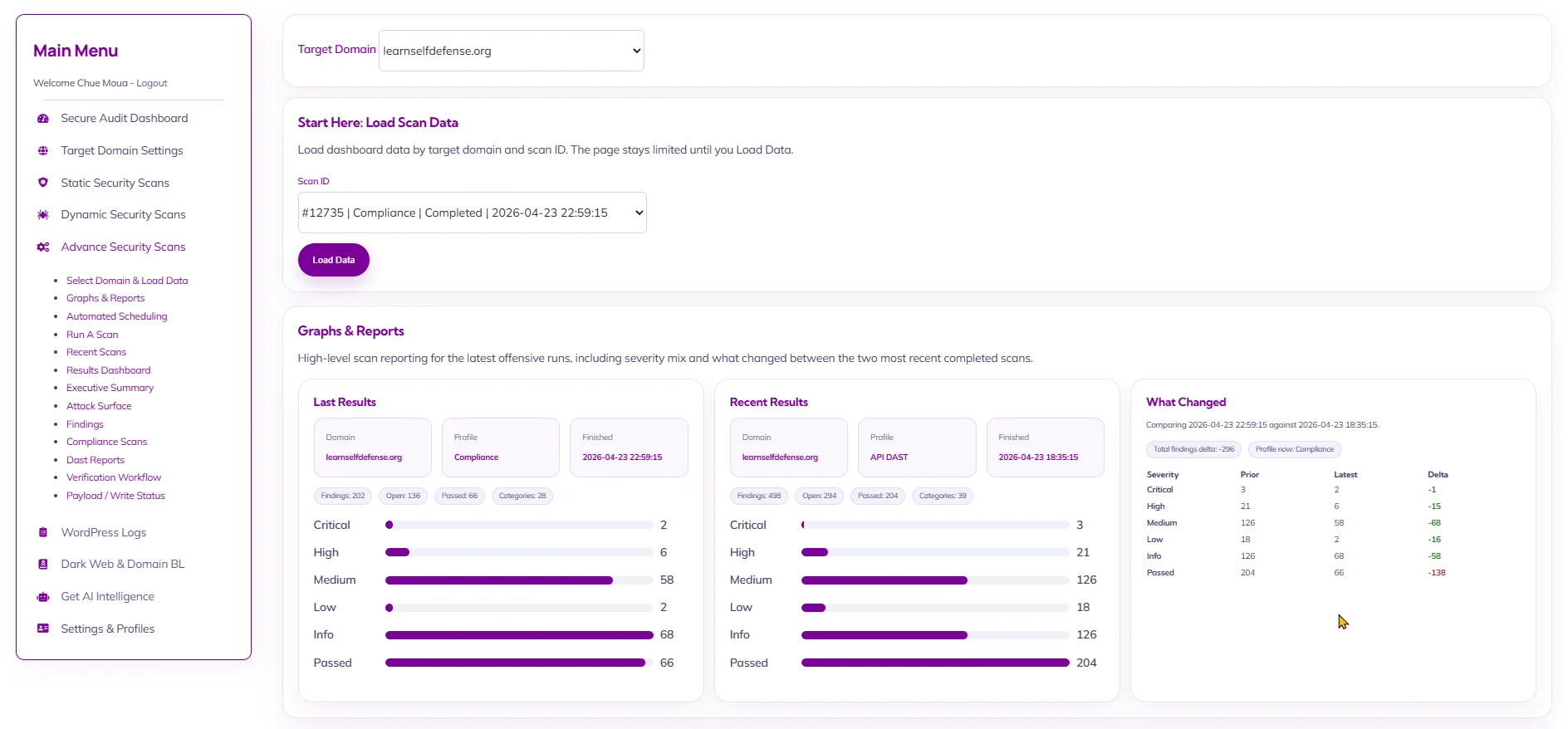
Reports, Risk Score, and Alerts
Security teams need evidence. Executives need clarity. Aegisify reports should connect severity, evidence, affected component, risk score, remediation status, and monitoring context. This helps turn scanner output into accountable work.
Security Scanner vs Audit Platform
| Capability | Basic Security Scanner | Aegisify Audit Direction |
|---|---|---|
| Plugin vulnerabilities | Shows a list of affected plugins. | Connects plugin and theme inventory to CVE context, fixed-version guidance, reports, risk score, and remediation planning. |
| Malware indicators | Checks files or signatures. | Adds context around backdoors, SEO spam, malicious redirects, blacklist status, logs, and cleanup guidance. |
| Exposed files | Flags public artifacts. | Explains why exposed files matter for attack surface, privacy, debugging leakage, and remediation priority. |
| DAST-style testing | Often limited or absent. | Reviews public attack surface, API hints, route behavior, headers, cookies, and payload family coverage where supported. |
| Reports | Generic scanner output. | Professional reports for security experts, engineers, site owners, executives, and agencies. |
| Remediation | Static advice. | Human-reviewable remediation guidance, verification steps, and monitoring. |
The first scan is only the beginning. WordPress risk changes whenever a plugin updates, a theme changes, a new user is added, a form is installed, a REST route appears, a debug log grows, or a vulnerability advisory is published. A scanner becomes more valuable when it supports continuous monitoring, alerts, reports, and historical scan comparison.
FAQ
What should a WordPress security scanner check?
A professional scanner should check known vulnerabilities, plugin and theme inventory, malware indicators, exposed files, blacklist status, security headers, cookies, login exposure, API hints, logs, alerts, reports, and remediation priorities.
Does a security scanner replace a firewall or WAF?
No. A scanner finds and prioritizes risk. A firewall or WAF helps block certain classes of traffic and attacks. Strong WordPress security usually requires scanning, protection, hardening, remediation, backups, and monitoring.
Should WordPress sites be scanned continuously?
Yes. WordPress risk changes as plugins, themes, users, logs, routes, and vulnerabilities change. Continuous monitoring and alerts help teams catch issues earlier.
Is Aegisify only for technical teams?
No. Aegisify should serve both technical and non-technical stakeholders by giving engineers useful evidence and giving executives, site owners, and marketing leaders a clear explanation of business impact.