WordPress Security Audit That Turns Risk Into Clear Action
A professional WordPress security audit should do more than identify technical issues. It should help executives, engineers, site owners, and cloud teams understand exposure, prioritize remediation, and monitor what changes over time.
What a WordPress Security Audit Means for Modern Teams
The Risk Model: Inventory, Exposure, Vulnerability, Evidence, and Remediation
Aegisify’s strongest marketing position is audit intelligence. The audit story should explain the relationship between five layers of security risk.
| Audit Layer | Why It Matters | Aegisify Audit Positioning |
|---|---|---|
| Inventory | Security starts with knowing what exists: WordPress core, plugins, themes, custom code, dependencies, users, and logs. | Aegisify helps organize plugin and theme inventory so risk is tied to real components, not assumptions. |
| Exposure | A component may be risky because of how it is reachable, publicly visible, or connected to login, checkout, APIs, or forms. | Aegisify supports public exposure review, exposed files checks, DAST-style analysis, API hints, and domain reputation workflows. |
| Vulnerability | Known plugin vulnerabilities, theme vulnerabilities, core vulnerabilities, CVEs, fixed versions, and dependency risk require structured review. | Aegisify helps connect component inventory to vulnerability scanner findings, CVE context, severity, and remediation priorities. |
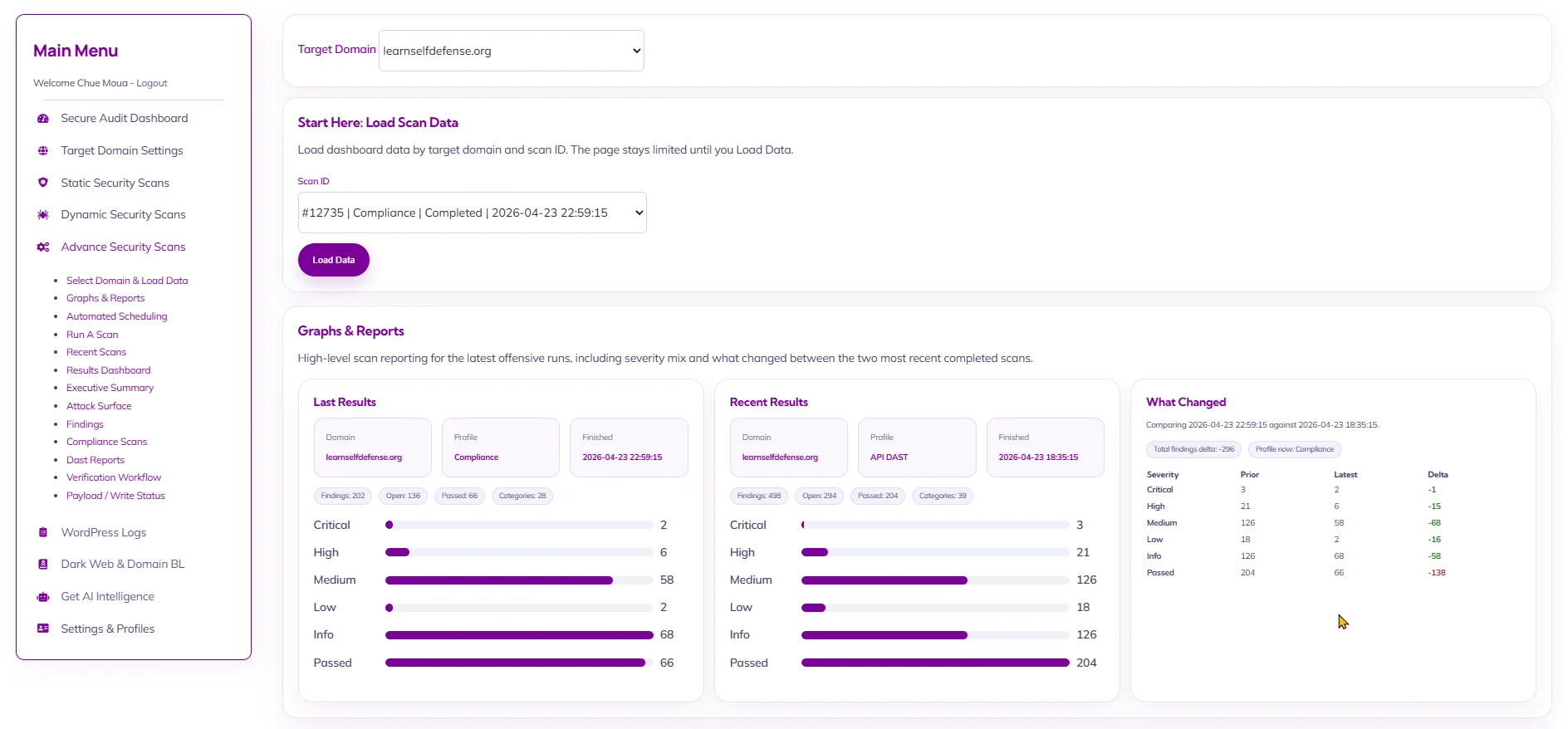
| Evidence | Executives and engineers need proof: logs, scan IDs, affected components, timestamps, reports, and historical status. | Aegisify uses target-domain and scan-ID workflows, WP Logging, App Logging, alerts, reports, and risk score context. |
| Remediation | Finding an issue is not enough. Teams need clear next steps, ownership, verification, and retesting. | Aegisify emphasizes human-reviewable remediation guidance, hardening direction, cleanup planning, and continuous monitoring. |
What Aegisify Audit Helps Review
Plugin, Theme, and Core Vulnerability Review
WordPress risk frequently begins with software sprawl. A business site may accumulate plugins, abandoned themes, custom snippets, WooCommerce extensions, marketing pixels, form integrations, caching layers, and third-party scripts over years. Aegisify helps review plugin vulnerabilities, theme vulnerabilities, core vulnerabilities, CVE references, fixed-version guidance, dependency risk, and the operational impact of vulnerable components.
This is useful for security experts who need vulnerability context, engineers who need a fix path, and executives who need a business-level explanation of why a component creates risk.
Plugin and Theme Inventory
A vulnerability scanner is only as useful as the inventory behind it. Aegisify’s audit story should make inventory a core value proposition. Plugin and theme inventory helps teams identify unused software, outdated components, unsupported themes, risky extensions, and components that may require removal instead of simple updates.
Static Code Analysis for Custom WordPress Risk
Many serious WordPress environments are not just brochure sites. They include custom plugins, WooCommerce modifications, membership flows, customer portals, API integrations, and custom business logic. Static code analysis helps flag risky code patterns and areas that require developer review. This gives application engineers a more practical starting point than a vague recommendation to “review custom code.”
DAST and Public Attack Surface Review
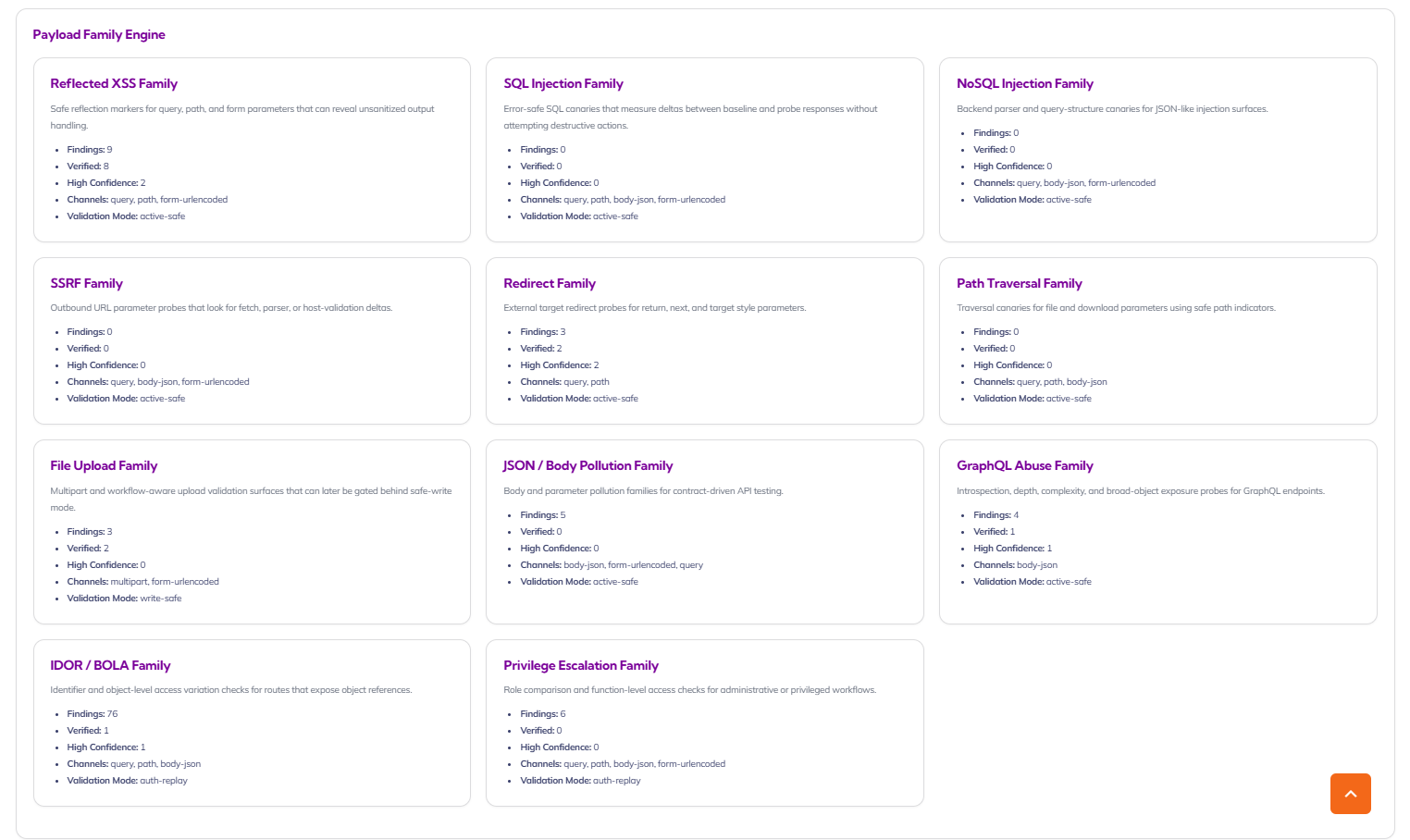
Aegisify offensive and advanced offensive workflows can be positioned around DAST-style analysis of the public surface: security headers, clickjacking posture, cookies, exposed WordPress artifacts, route discovery, API inventory, OpenAPI hints, GraphQL hints, and payload family coverage such as SQL injection, NoSQL injection, SSRF, and path traversal candidates.
The public copy should stay careful: Aegisify helps review and report DAST-style findings. It should not promise complete attack coverage or guaranteed exploitation prevention.
Malware Indicators, Backdoors, SEO Spam, and Malicious Redirect Signals
A security audit should include the signals that matter after compromise or suspected compromise: malware indicators, backdoors, blacklist status, SEO spam, malicious redirects, suspicious files, exposed files, unusual logs, and reputation changes. For public marketing, Aegisify should use responsible language such as “helps identify,” “helps review,” and “remediation guidance,” rather than claiming guaranteed cleanup.
WP Logging, App Logging, and Evidence Review
Logs are often where investigation becomes concrete. Aegisify can position WP Logging and App Logging as evidence layers that help explain what changed, when it changed, and what should be reviewed. This resonates with security engineers and cloud administrators because logs help connect scan findings to operational behavior.
AI Remediation Guidance With Human Review
AI remediation should be presented as a decision-support layer, not magic repair. The strongest claim is that Aegisify can help translate technical findings into human-reviewable remediation guidance, verification steps, and next-action planning. This is valuable for CEOs and site owners because it reduces confusion, and valuable for engineers because it helps organize the fix workflow.
Why a Basic Security Scanner Is Not Enough
A basic security scanner can identify individual issues. A mature WordPress security audit explains the relationship between issues. For example, an outdated plugin may become higher priority if it is active on checkout pages, has a public route, appears in logs, has a known CVE, and affects a high-value domain. The same issue may be lower priority if it is inactive, isolated, and scheduled for removal.
That distinction matters. Executives need prioritization. Engineers need details. Site owners need plain-English risk. Marketing leaders need to understand the SEO and brand risk of malware, SEO spam, blacklist status, malicious redirects, and Google penalties. Aegisify’s audit-intelligence position can bring those concerns into one workflow.
Aegisify Audit Workflow
1. Verify the target domain
A professional audit starts by tying findings to the right domain and account. This supports governance, reporting accuracy, and agency-style client workflows.
2. Choose the right scan profile
Teams can run security scans, vulnerability scans, static code analysis, offensive DAST-style reviews, advanced offensive reviews, logging workflows, domain reputation checks, and report generation based on the level of assurance needed.
3. Review evidence and risk score
Aegisify should help organize severity, affected component, evidence, status, category, business impact, and remediation priority in one reportable view.
4. Plan remediation
Remediation may mean updating, disabling, removing, hardening, investigating, applying WAF rules, cleaning suspicious files, involving a developer, or retesting after closure.
5. Monitor continuously
Security changes as WordPress core, plugins, themes, users, logs, APIs, and business requirements change. Continuous monitoring, alerts, reports, and scan history help reduce blind spots.
FAQ
Is a WordPress security audit the same as a vulnerability scanner?
No. A vulnerability scanner is one component of a complete WordPress security audit. A full audit should also review inventory, exposed files, DAST-style findings, logs, malware indicators, blacklist status, risk score, hardening, remediation, reports, and continuous monitoring.
Can Aegisify fix every security issue automatically?
No responsible security platform should promise that. Aegisify is best positioned as a platform that helps detect, prioritize, explain, recommend, and verify remediation. Some issues may support safe workflow automation, while others require developer, hosting, WAF, or cleanup review.
Does Aegisify replace a firewall or WAF?
No. A firewall or WAF is a protection layer. Aegisify Audit is an audit-intelligence layer that helps teams understand risk, evidence, reports, alerts, and remediation priorities. Aegisify WAF can be referenced separately when discussing active traffic protection.