How to Run a WordPress Security Audit
A WordPress security audit is a structured review of your website’s risk, configuration, software, code, public exposure, logs, and remediation priorities. It is not the same thing as installing a plugin and checking for alerts. A real audit asks better questions: what is exposed, what is outdated, what changed, what could be abused, what needs to be fixed first, and what evidence should be saved for the site owner, agency, or security team.
WordPress powers business websites, ecommerce stores, customer portals, membership sites, marketing hubs, and content platforms. That flexibility is powerful, but it also creates risk. Plugins, themes, custom code, REST API endpoints, login forms, file permissions, exposed debug logs, abandoned software, misconfigured headers, and WooCommerce workflows can all introduce security gaps.
Aegisify Audit is built to help teams approach that problem as an audit workflow. Instead of only showing isolated alerts, Aegisify Audit connects scan evidence, vulnerability findings, static code analysis, DAST-style checks, logs, compliance signals, and reporting into a clearer picture of site risk.
What Is a WordPress Security Audit?
A WordPress security audit reviews the technical and operational posture of a WordPress site. The goal is to identify weaknesses before they become incidents and to prioritize fixes based on risk.
A good WordPress security audit should review:
- WordPress core version
- Plugin and theme inventory
- Known vulnerabilities and CVEs
- User and admin exposure
- REST API exposure
- Login and authentication posture
- File and directory permissions
- Security headers
- HTTPS and TLS configuration
- Debug log exposure
- Malware indicators
- Suspicious admin users
- Public artifacts such as readme files, backups, database exports, or source maps
- WooCommerce checkout, cart, payment, order, webhook, and API surfaces
- Activity logs and application logs
- Compliance baseline signals
- Remediation priorities
Aegisify Audit helps organize these checks through a SaaS dashboard and connected WordPress Agent. The Agent gathers deeper WordPress-side information, while the SaaS dashboard helps present findings, reports, and AI-assisted recommendations.
Step 1: Create an Inventory of the Site
Start with inventory. You cannot secure what you cannot see.
Your audit should document:
- WordPress version
- Active plugins
- Inactive plugins
- Active theme
- Inactive themes
- Must-use plugins
- Custom plugins
- WooCommerce extensions
- REST API routes
- Forms
- Login surfaces
- Public pages
- Sensitive files
- Server and PHP signals where available
This inventory becomes the foundation for the entire audit. A WordPress plugin vulnerability scanner is only useful if it knows what plugins and versions are actually installed. A WordPress theme vulnerability scanner is only useful if it can identify active and inactive themes. A WordPress CVE scanner is only useful if it can map real software versions to known vulnerability intelligence.
Aegisify Audit’s Agent-side inventory helps support this step by collecting local WordPress information and making it available to the SaaS audit workflow.
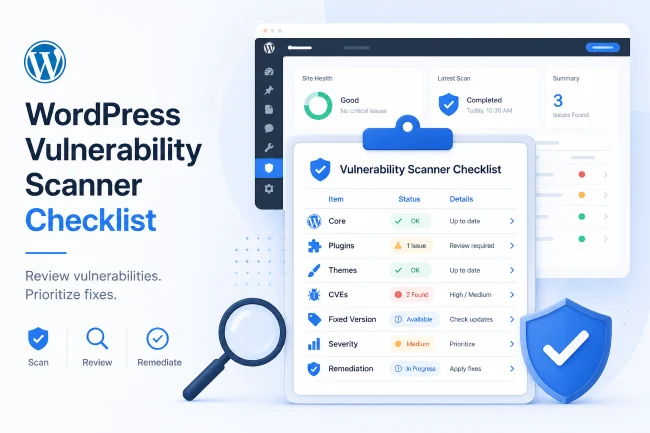
Step 2: Run a WordPress Vulnerability Scan
A WordPress vulnerability scanner checks whether your WordPress core, plugins, and themes are associated with known advisories. This is one of the fastest ways to find obvious risk, especially when plugins or themes are outdated.
A vulnerability scan should answer:
- Is WordPress core outdated?
- Are active plugins vulnerable?
- Are inactive plugins still risky?
- Are themes outdated or vulnerable?
- Is there a known fixed version?
- Is the vulnerability relevant to this site?
- Is the affected component active, inactive, or unused?
- Should the site patch, remove, replace, or monitor the component?
This is where Aegisify Audit becomes useful as more than a simple alert feed. The audit workflow can connect vulnerability data with inventory, risk context, and remediation guidance.
Step 3: Review the Public Attack Surface
A WordPress attack surface scanner looks at what is exposed to the public internet. This may include login pages, REST API routes, forms, scripts, source maps, install artifacts, exposed logs, backups, and sensitive paths.
Public exposure does not always mean a vulnerability exists. But exposure creates context. A public login page, exposed REST route, or readable artifact may become more important when combined with outdated software, weak access control, missing headers, or suspicious activity.
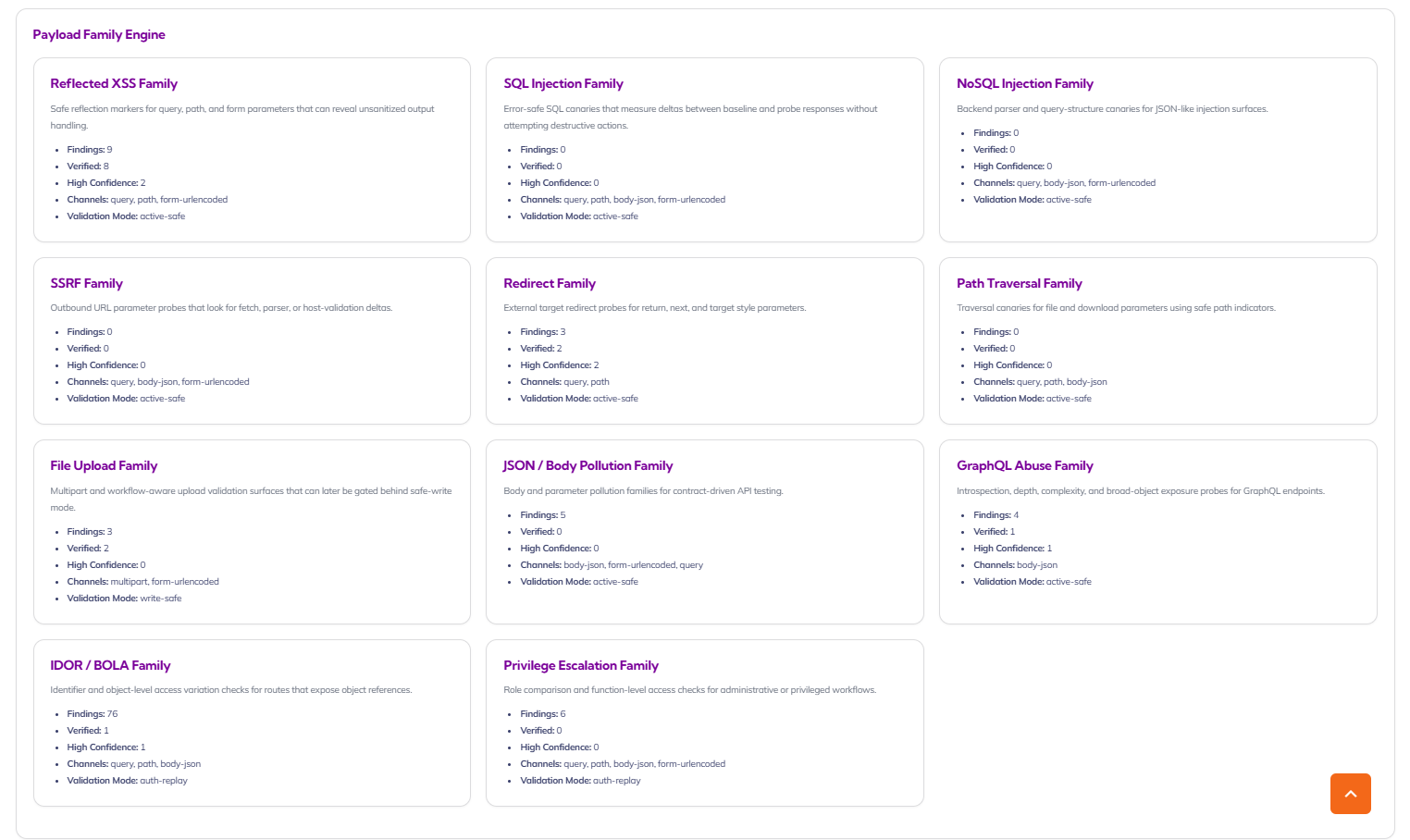
Aegisify Audit’s DAST-style profiles are designed to review public-facing behavior and help identify what deserves human review.
Step 4: Check REST API and Application Routes
The WordPress REST API is a normal part of modern WordPress. WordPress documentation states that the REST API provides endpoints representing posts, pages, taxonomies, and other built-in WordPress data types.
That does not mean every API exposure is bad. It means the audit should identify which routes exist, which are public, which require authentication, and whether custom plugins or WooCommerce extensions expose sensitive behavior.
A WordPress API security scanner should check:
- REST namespaces
- Custom plugin routes
- WooCommerce Store API exposure
- Authentication requirements
- Permission callbacks
- Public data returned by endpoints
- OpenAPI or GraphQL hints where present
- JavaScript-exposed routes
- Undocumented application routes
Aegisify Audit’s API DAST profile is built around REST, GraphQL, OpenAPI hints, browser/client-side signals, and application route inventory.
Step 5: Run Static Code Analysis
A WordPress static code analysis review looks at code without needing to exploit the site. It can help identify unsafe patterns, risky function usage, coding standard issues, plugin/theme logic weaknesses, and dependency risk.
Static analysis is especially valuable when a site uses:
- Custom plugins
- Custom themes
- Modified commercial plugins
- Agency-built functionality
- WooCommerce custom checkout logic
- Membership or portal code
- API integrations
Aegisify Audit’s Agent-side Static Code Analysis profile supports this workflow by running local review and returning structured findings for the SaaS dashboard.
Step 6: Review Logs
Security audits should not stop at scan results. Logs can show what changed, what failed, what was accessed, and what deserves follow-up.
Review:
- WordPress debug log
- Plugin/application logs
- WordPress activity log
- Admin changes
- Plugin/theme changes
- User changes
- Settings changes
- Fatal errors
- Authentication failures
- Suspicious requests
Aegisify Audit includes WP Logging and App Logging workflows so audit teams can evaluate logs alongside scan data.
Step 7: Build a WordPress Security Report
A WordPress security report should be written for humans, not just technicians.
Include:
- Executive summary
- Site risk overview
- Top findings
- Affected components
- Evidence
- Severity
- Business impact
- Recommended fix
- Owner
- Priority
- Status
- Retest date
Aegisify Audit helps turn noisy scan data into structured reporting, including downloadable report workflows and AI-assisted recommendations.
How Aegisify Audit Helps
Aegisify Audit helps site owners and agencies run security audits with a more complete workflow:
- Inventory collection
- Vulnerability scan
- Static code analysis
- DAST-style public exposure review
- API/REST/GraphQL review
- WooCommerce-oriented audit signals
- WordPress logs and activity logs
- Threat intelligence and reputation checks
- Compliance baseline signals
- AI-assisted remediation guidance
- Security reports
FAQ
How often should I run a WordPress security audit?
Run a full audit before major launches, after major plugin/theme changes, after WooCommerce changes, and on a recurring schedule for business-critical sites.
Is a WordPress security scanner enough?
A scanner helps, but a full audit should include inventory, vulnerabilities, code review, attack surface, logs, compliance signals, and remediation planning.
Can Aegisify Audit guarantee my site is secure?
No tool should promise that. Aegisify Audit helps identify, prioritize, and explain risk so teams can make better remediation decisions.