WordPress Vulnerability Scanner Checklist
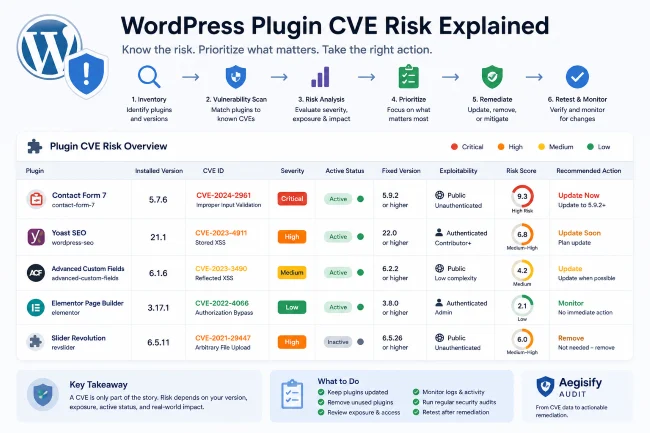
A WordPress vulnerability scanner helps you identify known security issues in WordPress core, plugins, themes, and related software. But the value of a vulnerability scanner is not just whether it finds a CVE. The real value is whether it helps you understand which finding matters, whether it applies to your site, what version fixes it, and what action should happen next.
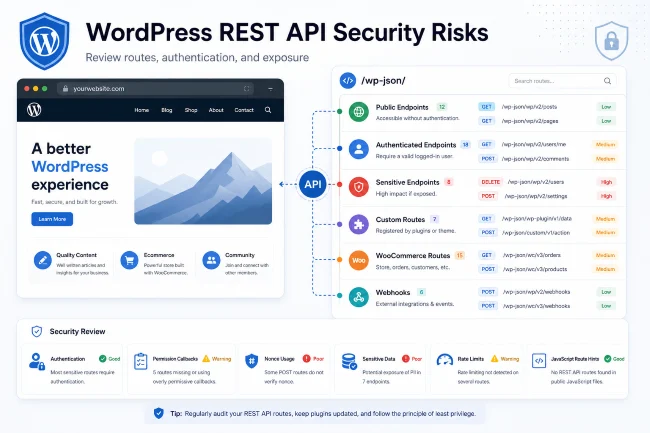
The National Vulnerability Database describes itself as a U.S. government repository of standards-based vulnerability management data, and CVE IDs provide unique identifiers for known vulnerabilities. For WordPress teams, this matters because plugins and themes can introduce risk even when the WordPress core itself is current.
Aegisify Audit helps turn vulnerability scanning into a WordPress security audit workflow by pairing software inventory, local Agent data, vulnerability matching, reports, and remediation guidance.
Why WordPress Vulnerability Scanning Matters
WordPress sites rely on many moving parts:
- WordPress core
- Plugins
- Themes
- Must-use plugins
- Composer packages
- JavaScript packages
- WooCommerce extensions
- Custom code
- Third-party integrations
A vulnerability in one plugin can create risk for the whole site. A vulnerable inactive plugin can still matter if the files remain accessible. A theme vulnerability can matter even if the theme is not visually obvious. A WooCommerce extension can expose business logic or data-handling risk.
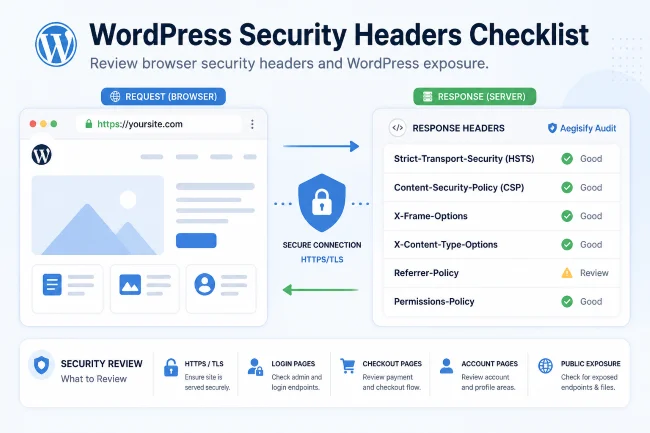
A good WordPress vulnerability scanner should help answer:
- What vulnerable software is installed?
- What version is affected?
- What version fixes the issue?
- Is the vulnerable component active?
- Is it internet-facing?
- Is it related to login, checkout, API, files, users, or admin actions?
- What should be patched, removed, replaced, or monitored?
Checklist: What a WordPress Vulnerability Scanner Should Review
1. WordPress Core Version
Start with the WordPress core version. The scanner should identify whether the installed version is current and whether any known vulnerabilities affect it.
The report should include:
- Current WordPress version
- Latest stable version
- Known advisories
- Fixed version
- Recommended action
Aegisify Audit uses inventory as the foundation for deeper vulnerability review.
2. Active Plugins
Active plugins deserve priority because their code is loaded and can affect the running site.
Review:
- Plugin name
- Plugin slug/file
- Installed version
- Active/inactive status
- Known advisories
- Fixed version
- Severity
- Exploitability context
- Business impact
A WordPress plugin vulnerability scanner should not simply produce a long list. It should help decide which plugin creates the most realistic risk.
3. Inactive Plugins
Inactive plugins are often ignored. That is a mistake. Inactive plugin files still exist on the server. Depending on the vulnerability and file exposure, they can still create risk.
Your checklist should ask:
- Are inactive plugins still needed?
- Are inactive plugins outdated?
- Are they abandoned?
- Are they vulnerable?
- Can they be safely removed?
Aegisify Audit can help inventory active and inactive plugins so site owners and agencies can reduce unnecessary attack surface.
4. Active Theme
Your active theme controls templates, front-end rendering, functions, and sometimes custom business logic. A WordPress theme vulnerability scanner should review the active theme and its version.
Check:
- Theme name
- Version
- Parent/child relationship
- Known vulnerabilities
- Custom modifications
- WooCommerce template overrides
- Update availability
5. Inactive Themes
Inactive themes should be reviewed and usually removed if they are not needed. Keep only what is required for rollback, child theme structure, or operational reasons.
6. Must-Use Plugins
Must-use plugins can be easy to forget because they do not behave like normal plugins in the WordPress admin. A serious audit should identify and review them.
7. WooCommerce Extensions
WooCommerce sites should receive extra attention because checkout, cart, payments, orders, customer accounts, and webhooks affect revenue and customer trust.
Review:
- Payment gateways
- Shipping plugins
- Subscription plugins
- Membership plugins
- Checkout customization plugins
- CRM integrations
- Tax and invoice plugins
Aegisify Audit’s commerce-oriented DAST workflow helps review WooCommerce-related surfaces when detected.
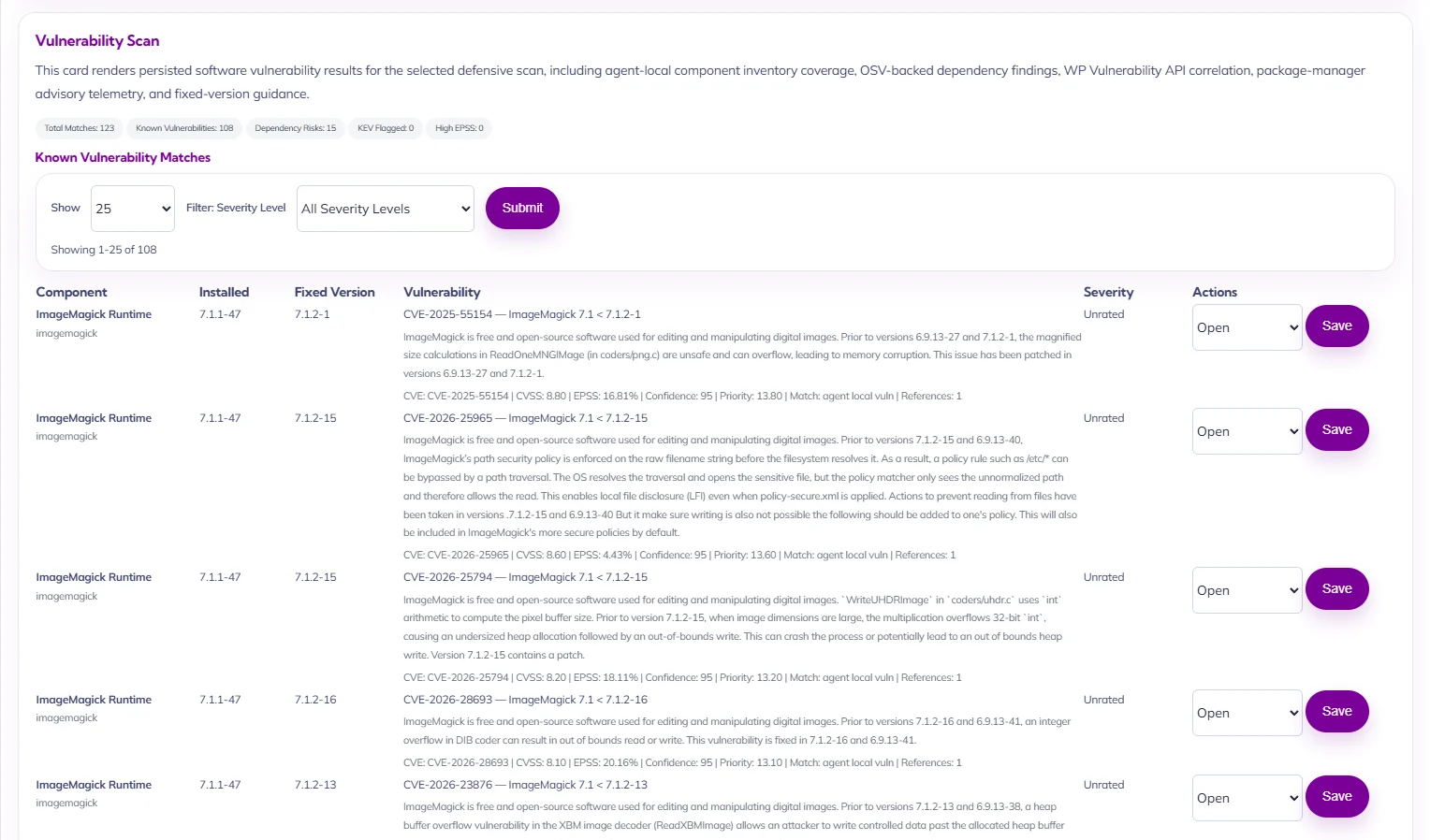
8. Fixed Version and Remediation Path
A vulnerability finding is incomplete without a fix path.
The scanner should tell you:
- What version is affected
- What version fixes it
- Whether update is available
- Whether removal is safer
- Whether replacement is needed
- Whether temporary mitigation is possible
- Whether retesting is required
How to Prioritize Vulnerability Findings
Not every vulnerability has the same urgency.
Prioritize based on:
- Severity
- Exploitability
- Whether the component is active
- Whether the vulnerable path is public
- Whether authentication is required
- Whether the component handles users, payments, files, orders, or admin actions
- Whether a fix exists
- Whether the site is business-critical
Aegisify Audit helps by connecting vulnerability results to broader audit context: inventory, public exposure, API routes, logs, and reports.
What Aegisify Audit Adds Beyond a Basic Scanner
A basic scanner may tell you that a plugin has a vulnerability. Aegisify Audit is designed to help answer what comes next.
It helps teams:
- Identify vulnerable WordPress components
- Connect findings to site inventory
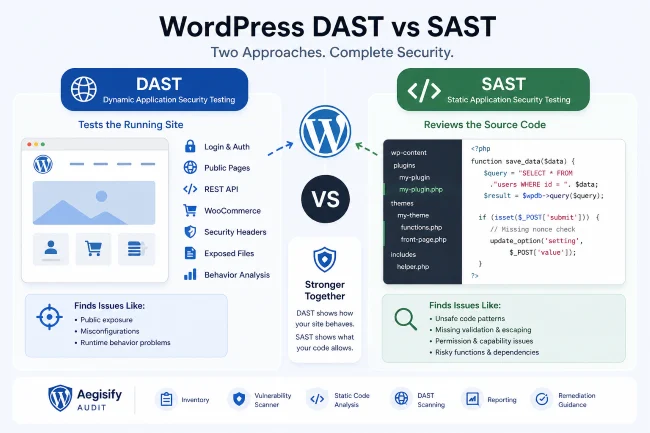
- Review defensive scan results
- Review static code analysis findings
- Review DAST-style exposure signals
- Generate reports
- Use AI-assisted recommendations for remediation planning
FAQ
What is a WordPress CVE scanner?
A WordPress CVE scanner checks whether installed WordPress software maps to publicly known vulnerabilities with CVE identifiers or other advisory records.
Should I remove inactive vulnerable plugins?
In many cases, yes. If an inactive plugin is not needed, removing it reduces unnecessary risk.
Is vulnerability scanning the same as malware scanning?
No. Vulnerability scanning checks known weaknesses in software. Malware scanning looks for malicious code, backdoors, suspicious patterns, or compromise indicators.