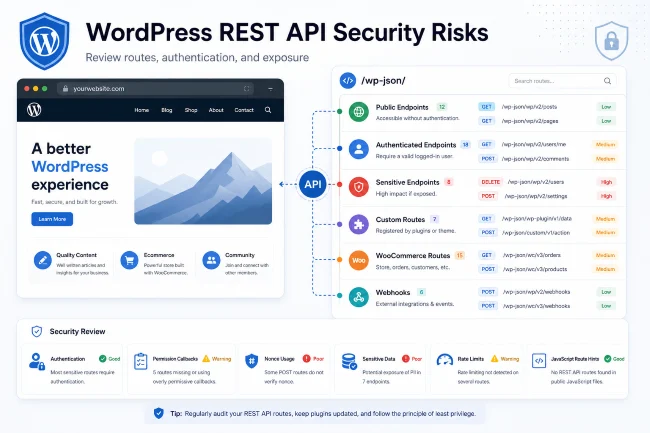
WordPress Plugin CVE Risk Explained
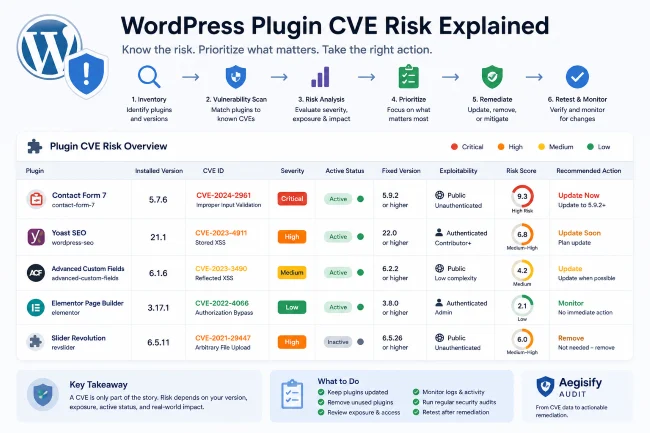
A CVE is not automatically an emergency, and it is not automatically harmless. It is a signal that a publicly identified vulnerability exists in a specific code base or component. For WordPress site owners, the important question is not only “does this plugin have a CVE?” The better question is “does this CVE apply to my installed version, my configuration, and my real attack surface?”
The CVE program provides unique identifiers for known vulnerabilities, and NVD provides standards-based vulnerability management data. But your WordPress site still needs context.
Aegisify Audit helps by connecting vulnerability intelligence to local WordPress inventory, scan results, attack-surface review, and remediation reporting.
What Is a WordPress Plugin CVE?
A WordPress plugin CVE is a public vulnerability identifier associated with a plugin or a dependency used by that plugin.
A CVE may involve:
- Broken access control
- SQL injection
- Cross-site scripting
- File upload flaws
- Privilege escalation
- Authentication bypass
- Sensitive data exposure
- Remote code execution
- Cross-site request forgery
- Insecure deserialization
Some CVEs are critical. Others require special conditions. Some only affect old versions. Some affect a feature you do not use. Some are actively exploited. Some have no known exploitation.
That is why prioritization matters.
Why Plugin CVE Risk Is Hard
WordPress plugin risk is complex because sites vary widely.
A plugin may be:
- Active
- Inactive
- Installed but unused
- Customized
- Abandoned
- Commercial
- Bundled inside a theme
- Required by WooCommerce
- Used only by admins
- Exposing public forms
- Exposing REST routes
- Handling payments or customer data
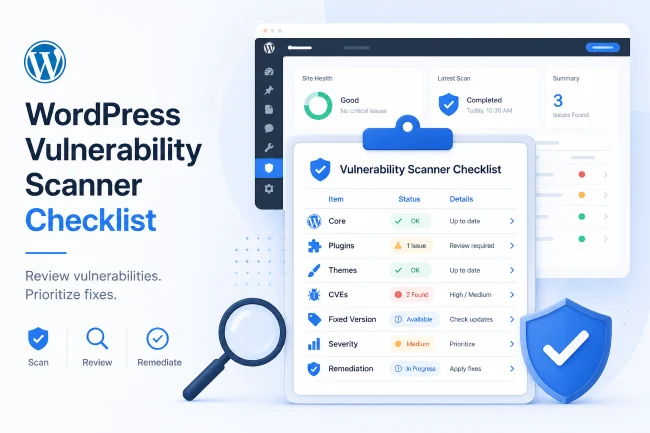
A WordPress plugin vulnerability scanner should not stop at “vulnerable.” It should help you understand relevance and urgency.
How to Prioritize WordPress Plugin CVEs
1. Confirm Installed Version
The first step is version matching.
Ask:
- What version is installed?
- What versions are affected?
- What version fixes the issue?
- Is the fixed version available?
2. Confirm Active Status
Active vulnerable plugins usually deserve more urgency. Inactive vulnerable plugins may still matter, but removal is often the cleanest fix.
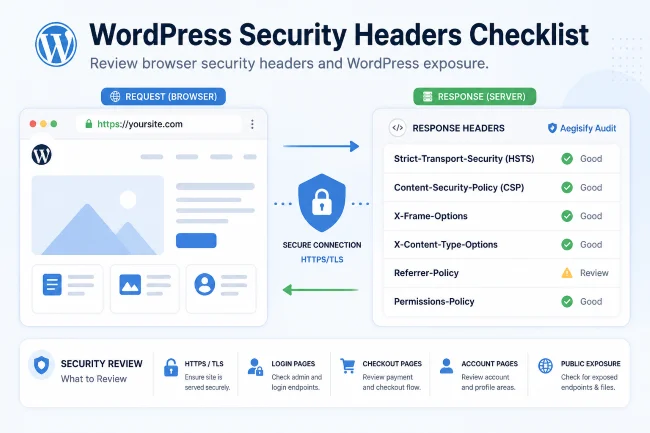
3. Review Public Exposure
A CVE is more urgent when the vulnerable feature is public or reachable.
Look for:
- Public forms
- REST routes
- AJAX actions
- File uploads
- Login-related behavior
- Checkout workflows
- Customer account workflows
- Webhook endpoints
4. Review Required Privileges
Some vulnerabilities require admin access. Others require subscriber access. Others require no authentication.
Unauthenticated vulnerabilities often deserve faster action because they are easier to reach.
5. Review Business Impact
A vulnerability touching orders, payments, users, files, or admin actions usually deserves higher priority than a low-impact issue in a rarely used feature.
6. Choose the Remediation Path
Options include:
- Update plugin
- Remove plugin
- Replace plugin
- Disable vulnerable feature
- Apply temporary mitigation
- Monitor logs
- Retest
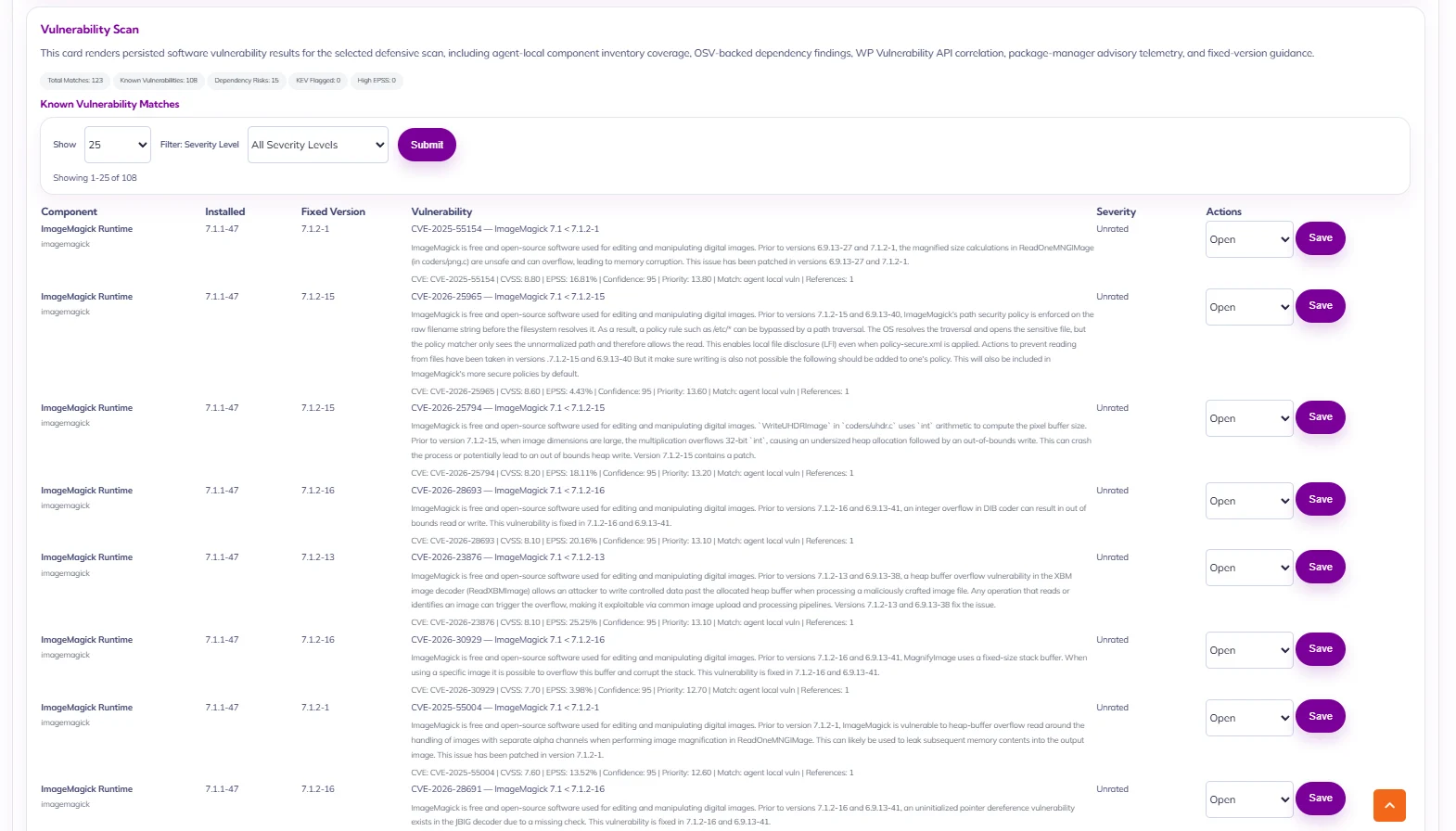
How Aegisify Audit Helps
Aegisify Audit helps teams move from raw vulnerability alerts to audit-ready decisions.
It supports:
- Plugin inventory
- Theme inventory
- Vulnerability scanning
- WordPress CVE scanner workflows
- WPVulnerability-style correlation when configured
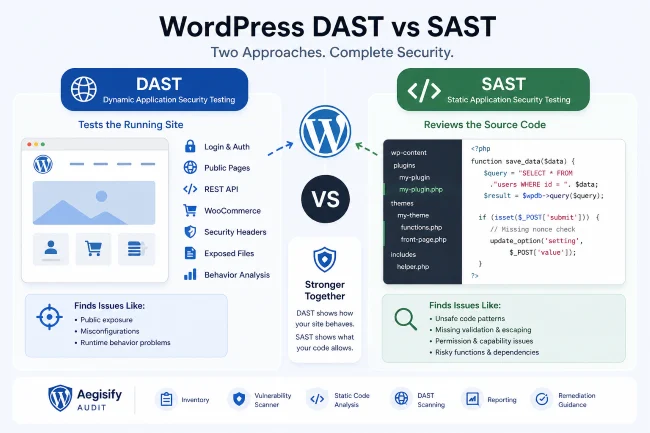
- Static code analysis
- DAST-style exposure review
- API surface review
- Logs and activity review
- Prioritized reports
This helps agencies explain plugin CVE risk to clients in practical terms.
Example Client-Friendly Explanation
“Your site has a plugin with a known vulnerability. The plugin is active and connected to a public form, so we recommend treating it as a high-priority update. After updating, we should retest the route and check the logs for suspicious activity.”
That is much more useful than: “Plugin vulnerable. Fix now.”
FAQ
Is every WordPress plugin CVE critical?
No. Severity depends on affected version, exploitability, authentication requirements, exposure, and business impact.
Should I delete vulnerable plugins?
If the plugin is unused, deletion may be safer than leaving it installed. If it is required, update or replace it.
Can Aegisify Audit explain CVE risk?
Aegisify Audit can help connect CVE-style findings with site inventory, scan evidence, and remediation planning.
Start With a Clear Security Picture
Use Aegisify Audit to turn WordPress scan data, logs, vulnerability findings, DAST-style evidence, risk score, alerts, and remediation planning into one professional workflow.
Try Aegisify Audit today!

Why security scan data becomes noisy so quickly
Every serious security expert knows the problem. A full audit can surface:
- configuration weaknesses
- exposed paths and endpoints
- risky behaviors
- repeated findings across similar routes
- medium and high severity items mixed with informational noise
- findings that sound technical but lack business context
Even when the scan engine is doing its job well, the output can still overwhelm the person reading it. That is not because the data is bad. It is because the data is dense.
 WordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth Gallery
WordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth GalleryWordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth
 2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified Gallery
2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified Gallery2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified
 2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud Gallery
2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud Gallery2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud
 WordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access Gallery
WordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access GalleryWordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access