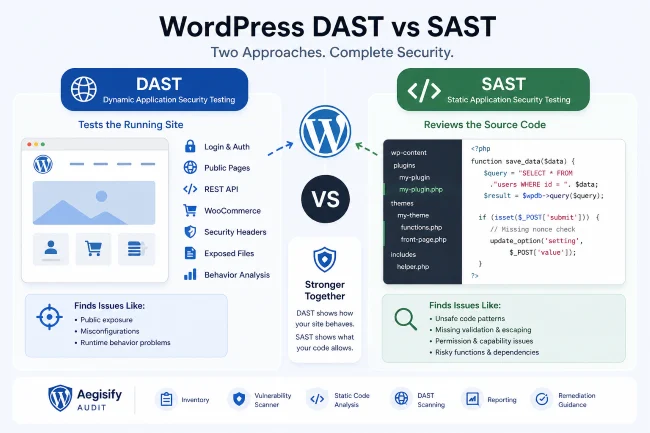
WordPress DAST vs SAST
DAST and SAST are two different ways to find security risk. For WordPress site owners, agencies, and WooCommerce operators, both matter.
DAST stands for dynamic application security testing. It evaluates a running site from the outside, similar to how a browser, visitor, or attacker might interact with public pages, forms, headers, login surfaces, APIs, and application behavior.
SAST stands for static application security testing. It reviews code without needing to execute the application. For WordPress, that can include plugins, themes, custom PHP, dependency files, and risky coding patterns.
Aegisify Audit uses both ideas in a WordPress-focused audit workflow: DAST-style public and application testing through SaaS scan profiles, and Agent-side static code analysis for local WordPress code review.
Why WordPress Needs Both DAST and SAST
WordPress security risk does not live in only one place.
Some issues only appear when the site is running:
- Missing security headers
- Public login exposure
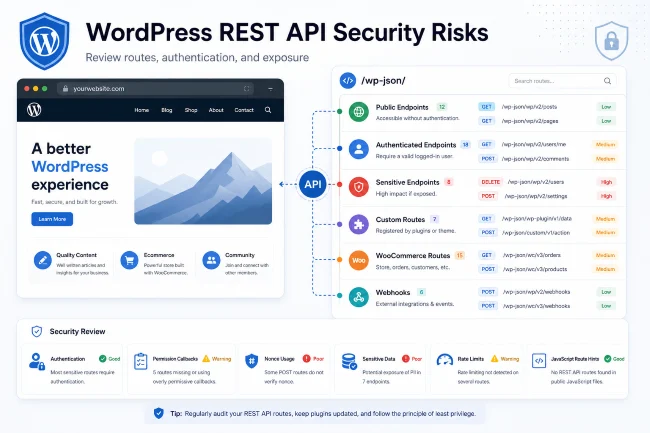
- REST API exposure
- Exposed files
- Public forms
- Source-map leaks
- Checkout behavior
- Session and authentication behavior
- Browser-facing JavaScript signals
Other issues are easier to find in code:
- Unsafe function usage
- Missing sanitization
- Missing escaping
- Permission callback mistakes
- Insecure file handling
- Risky custom plugin logic
- Coding standard problems
- Dependency risk
A WordPress DAST scanner and WordPress static code analysis process should work together. One shows how the site behaves. The other shows what the code may allow.
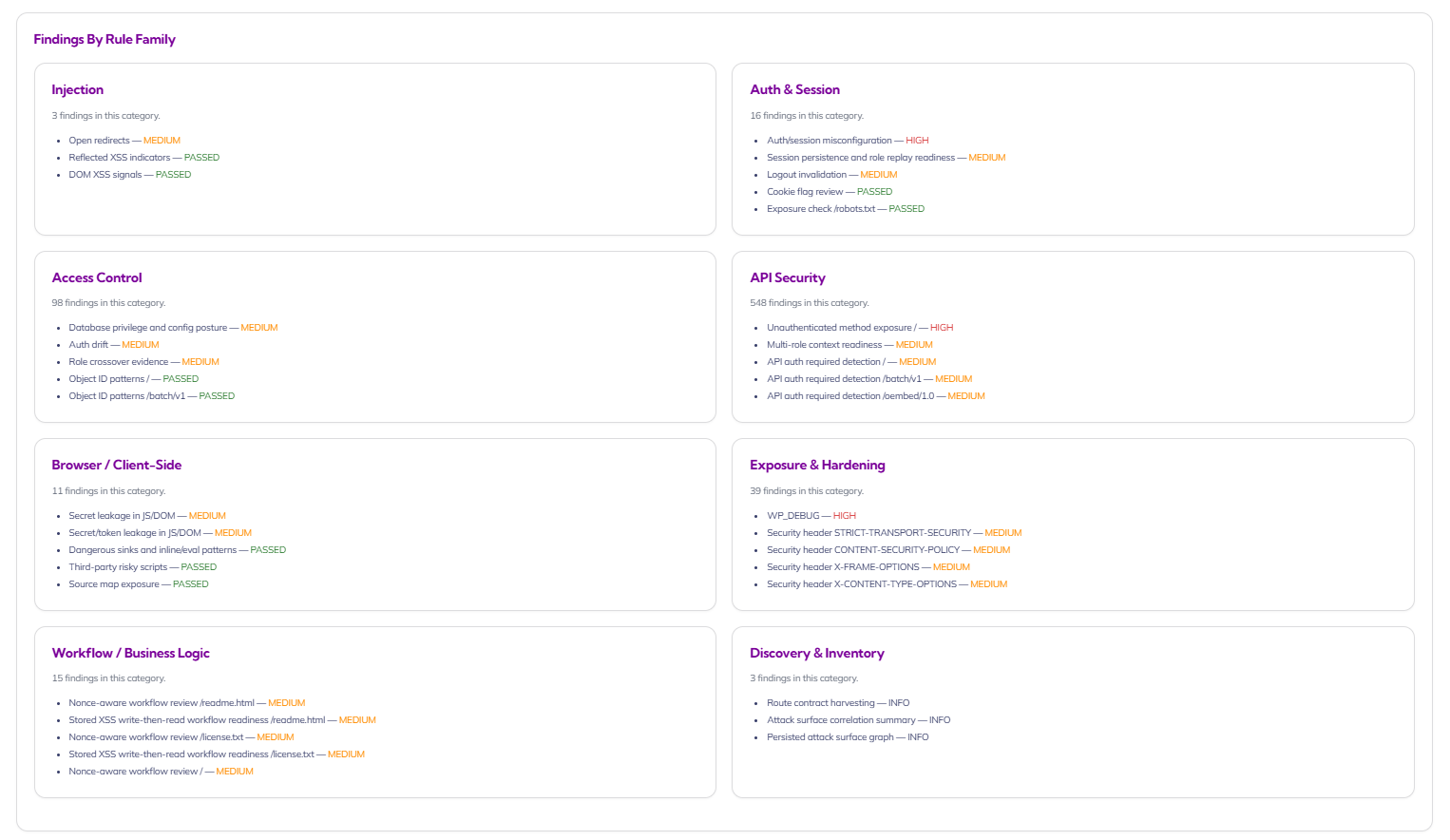
What a WordPress DAST Scanner Reviews
A WordPress DAST scanner evaluates the running website. It does not need to read source code to find useful signals.
A DAST-style audit may review:
- Public pages
- Forms and parameters
- Login surface
- REST API routes
- GraphQL endpoints where present
- OpenAPI hints where present
- Security headers
- Install artifacts
- Exposed debug logs
- Robots.txt hints
- Browser/client-side signals
- WooCommerce cart, checkout, order, payment, and webhook surfaces
OWASP describes the OWASP Top 10 as a standard awareness document for common web application security risks. DAST workflows often use OWASP-style categories because they help teams think about issues like access control, injection, misconfiguration, vulnerable components, and logging/monitoring gaps.
Aegisify Audit includes DAST-style profiles such as Quick DAST, Enterprise DAST: App & Commerce, Deep Auth DAST, and API DAST. These are designed around different levels of coverage and different site surfaces.
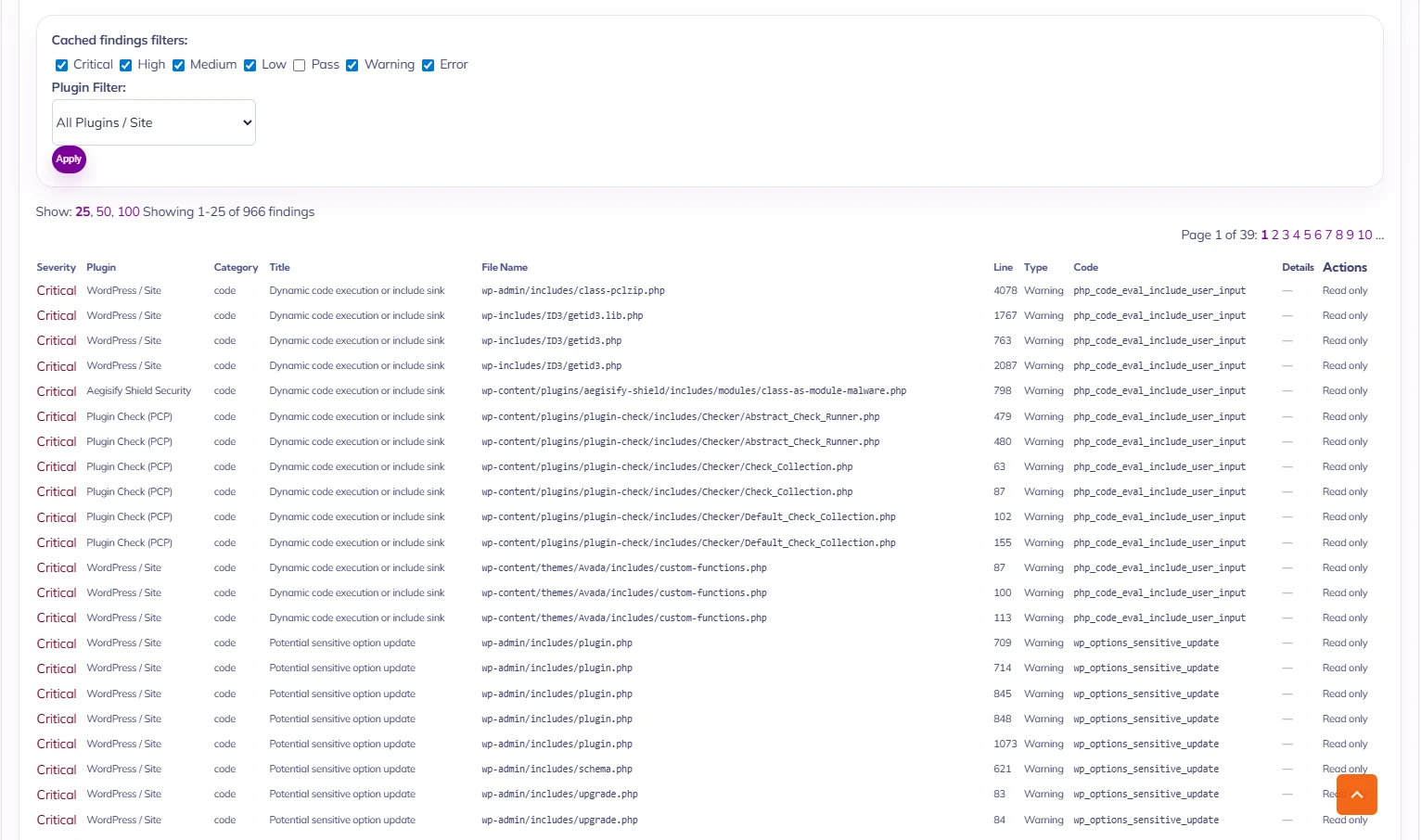
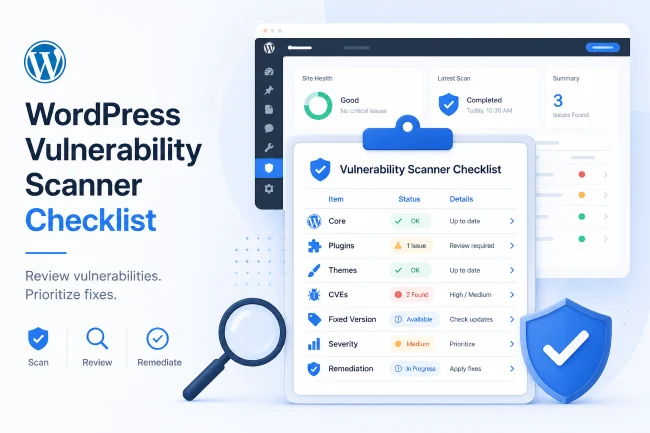
What WordPress Static Code Analysis Reviews
WordPress static code analysis reviews code and local files.
It may look for:
- Unsafe PHP patterns
- WordPress coding standard issues
- Missing escaping
- Missing sanitization
- Missing capability checks
- Weak nonce handling
- Risky file operations
- Dangerous dynamic SQL patterns
- Hardcoded secrets
- Risky dependency usage
- Plugin/theme quality issues
Static code analysis is especially important for:
- Custom plugins
- Custom themes
- Agency-built functionality
- WooCommerce customizations
- Membership sites
- Client portals
- Sites with private dashboards
- Sites using custom REST endpoints
Aegisify Audit’s Agent performs local static analysis and returns findings into the SaaS workflow so they can be reviewed alongside scan data and reports.
DAST vs SAST Comparison
| Area | DAST | SAST |
|---|---|---|
| Tests the running site | Yes | No |
| Reviews source code | No | Yes |
| Finds public exposure | Strong | Limited |
| Finds coding mistakes | Limited | Strong |
| Helps with API surface review | Yes | Sometimes |
| Helps with custom plugin review | Sometimes | Yes |
| Best for | Runtime behavior | Code-level risk |
| WordPress example | REST route exposed publicly | Permission callback missing in plugin code |
Why Agencies Should Care
Agencies often inherit sites they did not build. A client may have dozens of plugins, old custom code, outdated themes, or WooCommerce extensions that were installed years ago.
A DAST-only workflow may miss hidden code risk. A SAST-only workflow may miss runtime exposure. Together, they give a more complete audit picture.
Aegisify Audit is useful for agencies because it helps package that picture into a report a client can understand.
How Aegisify Audit Helps
Aegisify Audit helps combine:
- WordPress DAST scanner workflows
- WordPress static code analysis
- Vulnerability scanning
- Attack surface discovery
- API/REST/GraphQL review
- WooCommerce-specific review
- Logs and activity signals
- Compliance baseline signals
- AI-assisted remediation guidance
- Report generation
The result is not just a list of issues. It is a more structured WordPress security audit.
FAQ
Is DAST better than SAST?
No. DAST and SAST answer different questions. DAST reviews runtime behavior. SAST reviews code-level risk.
Does every WordPress site need static code analysis?
Sites with custom plugins, custom themes, WooCommerce customizations, or sensitive workflows benefit the most.
Can Aegisify Audit replace a human security review?
No. It helps collect, organize, and prioritize evidence so a site owner, developer, agency, or security reviewer can make better decisions.