WordPress Malware Indicators
WordPress malware is not always obvious. Some hacked sites display spam immediately. Others continue to look normal while attackers inject redirects, create hidden admin accounts, modify files, abuse SEO pages, or quietly collect data.
WordPress malware indicators are signs that a site may be compromised or at higher risk. They do not always prove malware exists, but they should trigger a security review.
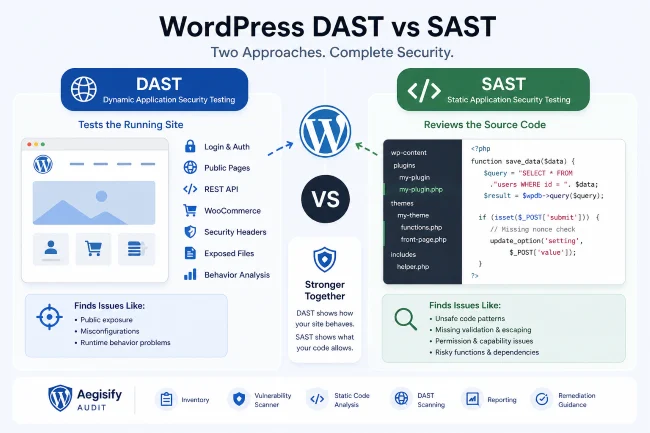
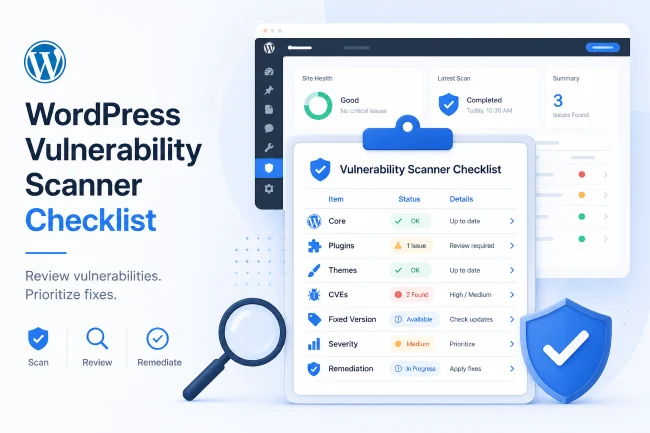
Aegisify Audit helps site owners and agencies review malware indicators as part of a broader WordPress security audit that includes vulnerability scanning, static code analysis, log review, activity logs, public exposure checks, and reporting.
Common WordPress Malware Indicators
1. Unexpected Redirects
If visitors are redirected to spam, adult content, fake updates, gambling pages, crypto pages, or suspicious downloads, the site may be compromised.
Check:
.htaccesswp-config.php- Theme files
- Plugin files
- JavaScript injections
- Database options
- Header/footer scripts
- Unknown mu-plugins
- Redirect plugins
- CDN/page rules
2. Strange Search Results
A site may look normal in the browser but show spam titles or descriptions in Google or Bing. This is often called SEO spam.
Search indicators include:
- Japanese keyword spam
- Pharma spam
- Casino/gambling pages
- Fake product pages
- Injected indexed URLs
- Strange meta titles
- Cloaked content
Aegisify Audit’s security and SEO-adjacent audit workflow can help identify suspicious site signals and connect them to remediation planning.
3. Unknown Admin Users
Unexpected admin users are a serious warning sign.
Review:
- User list
- Recently created admins
- Unknown emails
- Weak usernames
- Privilege escalation indicators
- Activity log events
- Plugin/theme changes after account creation
Aegisify Audit’s Agent-side activity logging can help review user and admin changes when available.
4. Modified Core Files
WordPress core files should not contain unexpected modifications. If core files changed outside normal updates, investigate.
Review:
- Core integrity
- Recently modified files
- Unknown PHP files
- Suspicious includes
- Base64-like obfuscation
- Eval-like behavior
- Unusual file names
5. Suspicious Plugin or Theme Files
Malware often hides inside plugin or theme directories because those directories already contain PHP files.
Look for:
- Random file names
- Recently modified PHP files
- Obfuscated code
- Files in upload directories
- Unknown plugin folders
- Hidden backdoor files
- Modified theme functions
Aegisify Audit’s static code analysis can help identify suspicious code patterns for review.
6. Exposed Debug Logs
A public debug.log can leak paths, errors, plugin names, stack traces, database details, or security-sensitive information. Even if it is not malware, it can help attackers understand the site.
Aegisify Audit includes WP Logging workflows to help collect and review debug and activity information.
7. Blacklist or Reputation Warnings
A site may be flagged by search engines, browsers, email providers, or security services.
Review:
- Google Search Console security issues
- Browser warnings
- Email deliverability issues
- Domain blacklist status
- Suspicious outgoing links
- Unwanted indexed pages
Aegisify Audit’s threat intelligence workflow can support domain reputation and blacklist-style review, depending on configured providers.
8. Unusual Server Resource Usage
High CPU, unknown cron jobs, sudden traffic spikes, or outgoing requests may indicate abuse.
Check:
- Cron events
- Scheduled tasks
- Unknown plugins
- Logs
- Hosting resource graphs
- Outbound requests
- PHP errors
What to Do When You See Malware Indicators
Do not panic. Do not randomly delete files without a backup. Follow a controlled process:
- Put the site into a safe operational state.
- Take a backup for investigation.
- Review users and access.
- Run a WordPress security scanner.
- Run a WordPress vulnerability scanner.
- Review logs.
- Review changed files.
- Inspect suspicious plugins and themes.
- Remove confirmed malware.
- Patch vulnerable components.
- Rotate passwords and keys.
- Retest.
- Monitor after cleanup.
How Aegisify Audit Helps
Aegisify Audit helps by connecting multiple signals:
- Vulnerability findings
- Static code analysis
- Malware indicator review
- WordPress activity logs
- Debug log review
- Public exposure checks
- Threat intel and reputation checks
- Reports and remediation guidance
Aegisify Audit does not need to claim “one-click guaranteed cleanup” to be valuable. Its strength is helping teams see what matters and prioritize safe remediation.
FAQ
Are malware indicators proof my site is hacked?
Not always. They are signals that deserve investigation.
Should I restore from backup immediately?
Not always. If the backup also contains malware or the vulnerable entry point still exists, the site may be reinfected.
Can Aegisify Audit remove all malware automatically?
No public copy should promise that. Aegisify Audit helps identify, organize, and prioritize security evidence for human-reviewable remediation.