WooCommerce Security Audit Checklist
A WooCommerce security audit reviews the security posture of a WordPress ecommerce store. It goes beyond checking whether WordPress is updated. A real WooCommerce audit looks at plugins, checkout flow, payment-related logic, customer accounts, REST API exposure, order workflows, webhooks, logs, and remediation priorities.
WooCommerce stores carry higher business risk than brochure sites because they handle revenue, customers, orders, payments, refunds, coupons, accounts, subscriptions, and integrations. A small configuration mistake or vulnerable plugin can affect trust and operations.
Aegisify Audit includes Enterprise DAST: App & Commerce workflows designed to review application and commerce surfaces when they are detected, including checkout, cart, payment, webhook, order, and compatibility signals.
Why WooCommerce Security Is Different
A normal WordPress site may focus on content, forms, and logins. A WooCommerce store adds business logic.
You need to review:
- Cart behavior
- Checkout behavior
- Payment gateway integration
- Order data exposure
- Customer account security
- Coupon and discount logic
- Webhooks
- API routes
- Shipping and tax plugins
- Subscription logic
- Membership integration
- Refund and order status workflows
- Admin access
- Logs and error events
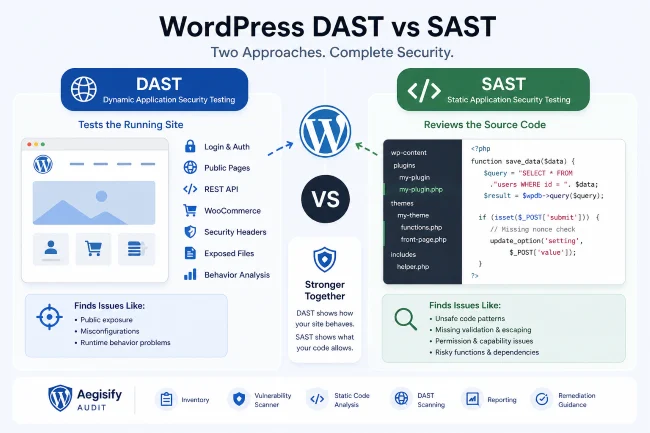
This is why a WooCommerce security audit should combine a WordPress vulnerability scanner, WordPress API security scanner, DAST-style review, static code analysis, and log review.
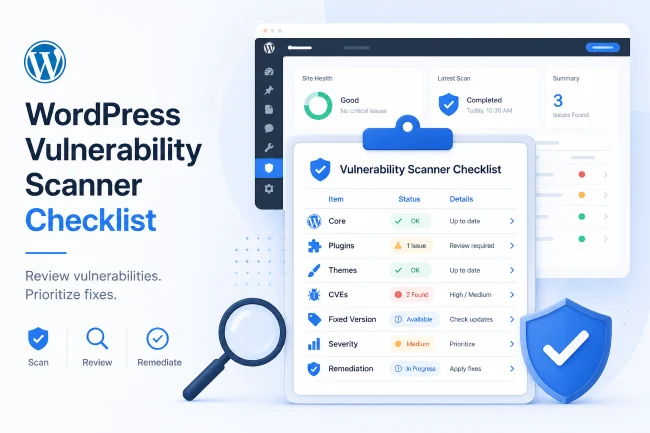
Checklist: What to Review
1. WooCommerce Core and Extensions
Document the installed versions of:
- WooCommerce
- Payment gateways
- Shipping plugins
- Subscription plugins
- Membership plugins
- Checkout field editors
- Invoice plugins
- Tax plugins
- CRM integrations
- Fulfillment plugins
- Custom WooCommerce extensions
Then review each for known advisories, update status, active/inactive state, and business importance.
2. Checkout and Cart Flow
Checkout is the revenue path. Review:
- Cart token behavior
- Nonce/token signals
- Guest checkout settings
- Account creation behavior
- Payment redirection
- Error handling
- Coupon handling
- Shipping calculation
- Tax calculation
- Custom fields
- JavaScript behavior
- Sensitive data leakage
Aegisify Audit’s commerce DAST workflow can help identify checkout and cart surfaces that deserve review.
3. Payment Gateway Configuration
A security audit should not claim PCI compliance unless validated by a qualified process. But it can still review payment-related configuration signals.
Check:
- Whether card data is handled directly or by a payment provider
- Whether payment pages use HTTPS
- Whether gateway plugins are current
- Whether test mode is disabled in production
- Whether webhook secrets are configured
- Whether payment logs expose sensitive information
4. Customer Account Security
Review:
- Registration settings
- Password reset flow
- Login exposure
- Admin users
- Customer role permissions
- Account endpoint behavior
- User enumeration signals
- Suspicious admin or customer accounts
- Recent account changes
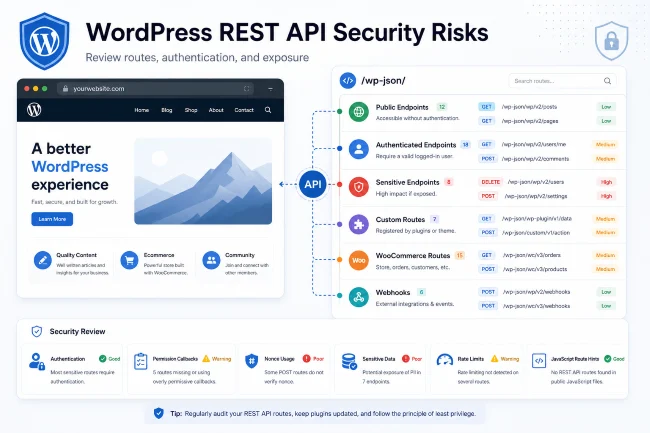
5. WooCommerce REST and Store API
WooCommerce uses APIs for modern store behavior. These APIs should be reviewed for intended exposure.
Check:
- Store API routes
- REST routes
- Custom extension routes
- Order-related endpoints
- Customer-related endpoints
- Webhook endpoints
- Authentication requirements
- Public response data
- JavaScript-exposed routes
Aegisify Audit’s API DAST workflow helps review REST, OpenAPI hints, GraphQL hints, and JavaScript-exposed routes where present.
6. Logs and Activity
Review:
- WooCommerce logs
- WordPress debug log
- Payment gateway logs
- Failed order logs
- Webhook failures
- Admin changes
- Plugin/theme changes
- User changes
- Fatal errors
Aegisify Audit includes WP Logging and application log workflows so teams can review operational evidence alongside scan findings.
7. Security Headers and HTTPS
Review:
- HTTPS active
- Mixed content
- HSTS
- Content Security Policy where appropriate
- X-Frame-Options or frame-ancestors
- Referrer-Policy
- Permissions-Policy
Security headers will not fix vulnerable plugins, but they help reduce browser-facing risk.
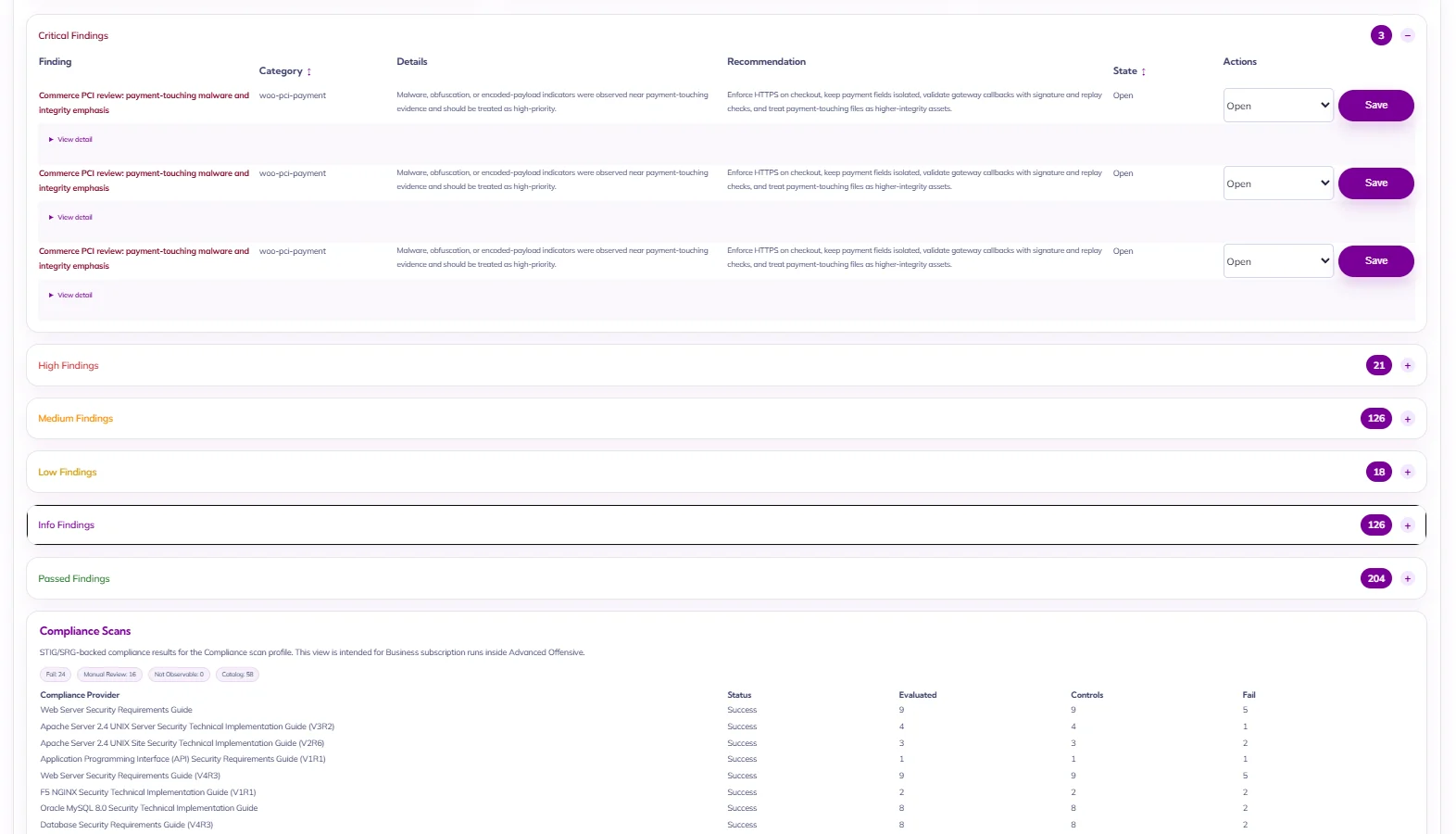
How Aegisify Audit Helps WooCommerce Teams
Aegisify Audit helps WooCommerce operators and agencies:
- Inventory store plugins and extensions
- Identify known vulnerable components
- Review checkout and payment-related surfaces
- Inspect REST/API exposure
- Review public attack surface
- Correlate logs and scan evidence
- Generate security reports
- Prioritize remediation
The goal is not to scare store owners. The goal is to protect revenue and customer trust by giving teams a clearer view of what needs attention.
FAQ
How often should I run a WooCommerce security audit?
Run one before major store launches, payment changes, checkout changes, new extension installs, and on a recurring schedule for active stores.
Is WooCommerce secure by default?
WooCommerce can be run securely, but store risk depends on plugins, configuration, hosting, user access, custom code, payment setup, and maintenance.
Can Aegisify Audit guarantee PCI compliance?
No. Aegisify Audit can support review and remediation planning, but compliance claims require proper validation and scope.