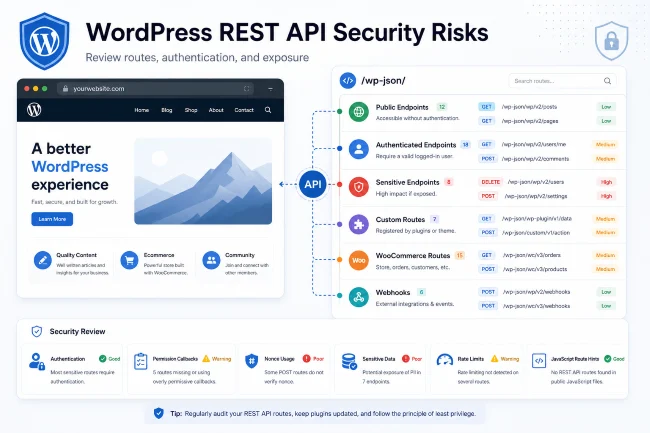
WordPress REST API Security Risks
The WordPress REST API is not automatically a security problem. It is a normal part of modern WordPress. WordPress documentation explains that the REST API provides endpoints representing posts, pages, taxonomies, and other built-in WordPress data types, and that applications can send and receive JSON through those endpoints.
The risk comes from misunderstanding what is exposed, adding custom routes without proper permission checks, exposing sensitive data, or assuming that hiding a route is the same as securing it.
A WordPress API security scanner helps site owners and agencies identify REST routes, custom endpoints, authentication requirements, public data, and API-related attack surface.
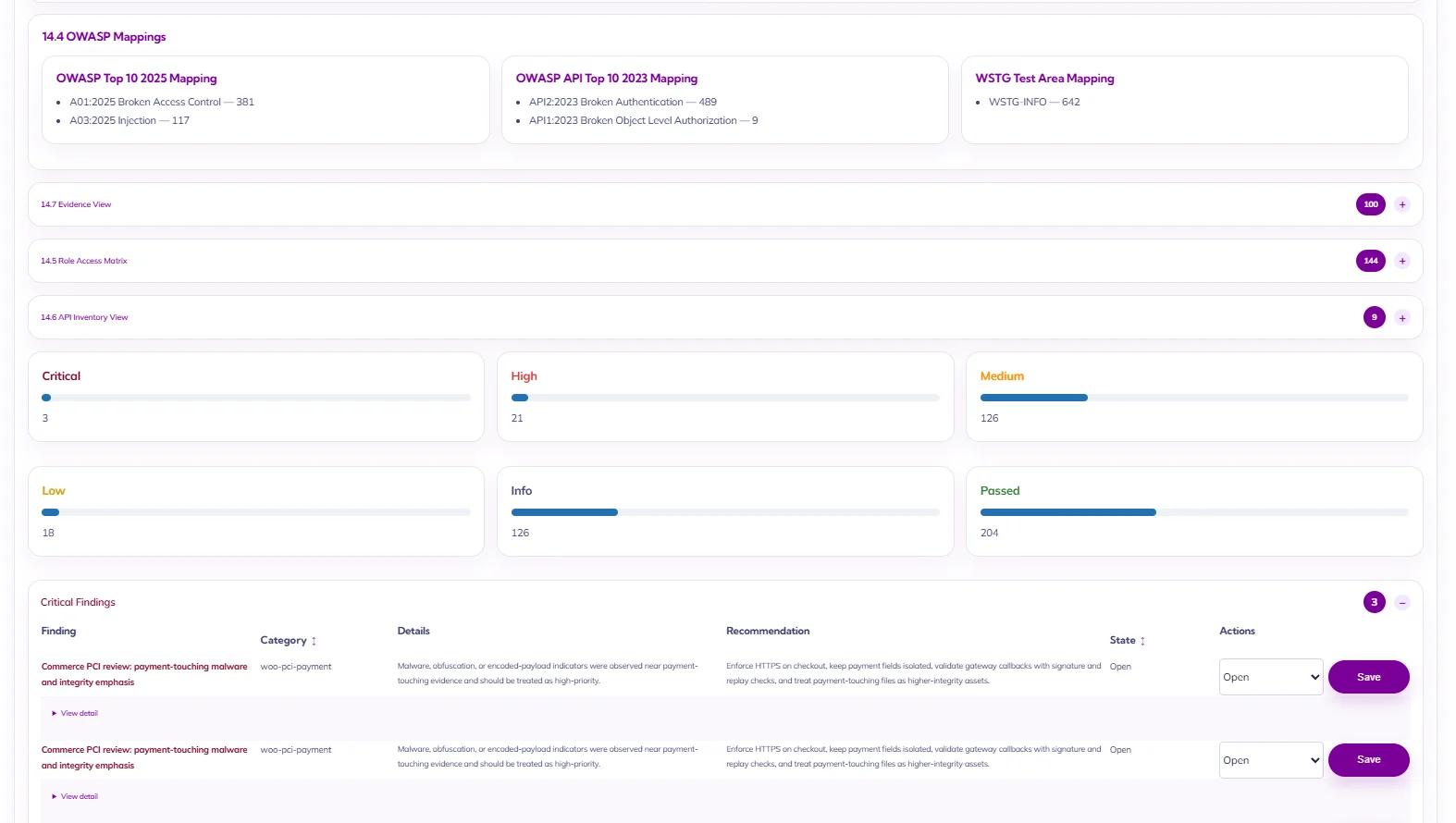
Aegisify Audit includes API DAST and attack-surface review workflows designed to help teams inspect REST, GraphQL, OpenAPI hints, JavaScript-exposed routes, browser/client-side signals, and API inventory evidence.
Why REST API Security Matters
Modern WordPress sites are more than simple blogs. Many use WordPress as:
- A marketing CMS
- WooCommerce store
- Membership platform
- Customer portal
- Headless CMS
- LMS
- Booking system
- Directory
- Internal tool
- Content API
That means plugins and themes may create custom REST endpoints. Some are harmless. Some may expose sensitive data, weak permissions, or business logic risk.
A WordPress security audit should identify what API routes exist and whether they match the site’s intended exposure.
Common WordPress REST API Risks
1. Public Routes Returning Too Much Data
Some endpoints are meant to be public. Others should not be. The audit should check whether public routes expose:
- User data
- Order data
- Customer data
- Private post data
- Internal IDs
- Email addresses
- Plugin configuration
- Debug details
- File paths
- Sensitive metadata
Public data exposure can be especially important on WooCommerce, membership, and portal sites.
2. Weak Permission Callbacks
Custom REST routes should have clear permission logic. A route that modifies settings, reads private data, exports records, or performs admin actions should not be available to anonymous users or low-privilege accounts.
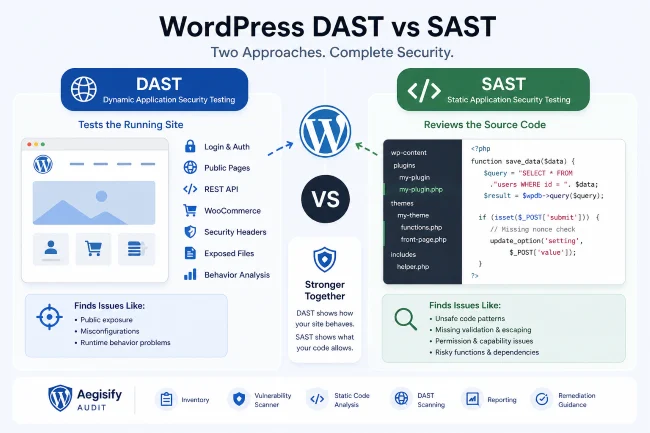
Aegisify Audit’s API and static analysis workflows are useful together here: DAST can help identify route exposure, while static code analysis can help review code-level permission patterns.
3. Authentication Assumptions
WordPress documentation says cookie authentication is the standard authentication method included with WordPress. But not every API use case should rely on assumptions about login state. Sites using application passwords, custom auth, third-party integrations, or headless front ends should review authentication and authorization carefully.
4. JavaScript-Exposed Routes
Front-end JavaScript can reveal API paths, nonces, parameters, and workflow hints. That does not automatically mean a vulnerability exists. But it gives an auditor useful information about what the application exposes.
Aegisify Audit’s API DAST workflow looks at JavaScript-exposed and undocumented routes as part of broader API discovery.
5. WooCommerce Store API Exposure
WooCommerce sites have legitimate API surfaces for cart, checkout, products, customer accounts, and orders. These routes should be reviewed for intended exposure, authentication, rate limiting, and data handling.
For ecommerce sites, API security is not only a technical issue. It affects revenue, customer trust, and operational risk.
6. GraphQL and OpenAPI Hints
Some WordPress sites use GraphQL plugins or publish OpenAPI-style documentation. These can help development teams, but they also make the API surface easier to understand.
Aegisify Audit’s advanced API workflow can review REST, GraphQL, and OpenAPI hints where detected.
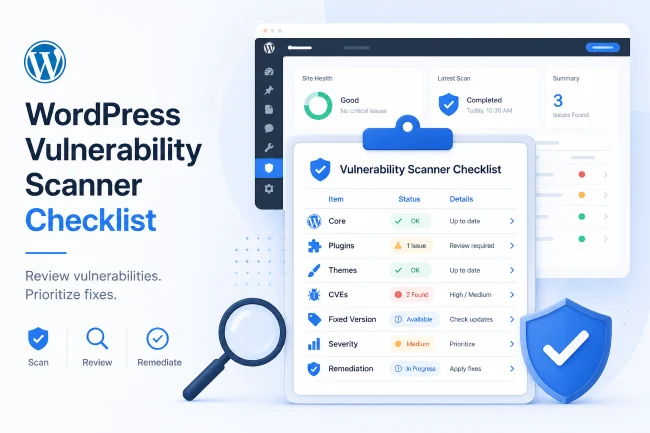
WordPress API Security Checklist
Review:
- REST namespaces
- Public endpoints
- Authenticated endpoints
- Custom plugin routes
- WooCommerce routes
- User/account routes
- File upload/download routes
- Export/reporting routes
- Bulk action routes
- Webhook routes
- Permission callbacks
- Nonce usage
- Authentication method
- Sensitive response data
- Rate-limit concerns
- Error messages
- Debug data
- JavaScript-exposed route hints
How Aegisify Audit Helps
Aegisify Audit helps teams inspect API risk as part of a larger WordPress security audit.
It supports:
- REST surface discovery
- API DAST profile
- JavaScript-exposed route review
- GraphQL and OpenAPI hint detection
- WooCommerce/API surface review
- Static code analysis for custom code patterns
- Reporting and prioritization
This helps site owners move from “we have REST routes” to “we know which routes exist, what they expose, and what should be reviewed.”
FAQ
Should I disable the WordPress REST API?
Not usually. Many WordPress features, plugins, and editors rely on it. The better approach is to review exposure, permissions, and data returned by endpoints.
Is every public REST route dangerous?
No. Public routes are normal. The question is whether they expose sensitive data or behavior.
What is a WordPress API security scanner?
It is a scanner that helps identify API routes, public exposure, authentication requirements, and possible API-related risk in a WordPress site.