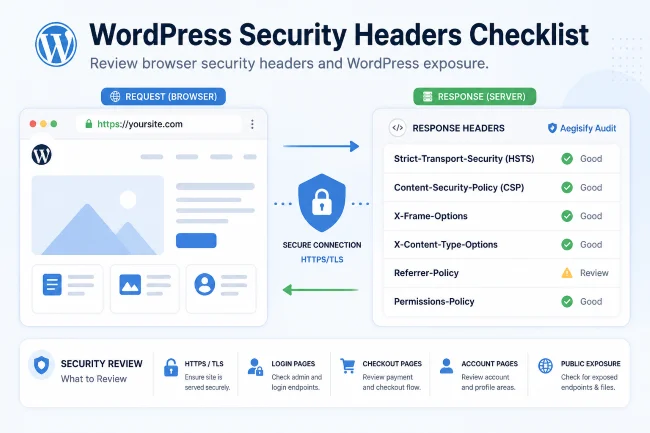
WordPress Security Headers Checklist
Security headers help browsers enforce safer behavior when visitors load your WordPress site. They are not a replacement for patching, secure coding, vulnerability management, or access control, but they are an important part of a WordPress security audit.
A WordPress security scanner should review headers because missing or weak headers can increase exposure to clickjacking, mixed content, data leakage, browser feature abuse, and script-related risk.
Aegisify Audit’s DAST-style workflows include header and public exposure checks as part of a broader WordPress security audit.
Why Security Headers Matter
Browsers make security decisions based on headers returned by the server. These headers can help define:
- Whether the site should only use HTTPS
- Whether the page can be framed
- Which scripts are allowed
- How much referrer information is sent
- Which browser features are allowed
- Whether MIME sniffing is blocked
Security headers are especially important for:
- Login pages
- Checkout pages
- Account pages
- Admin-adjacent workflows
- Membership portals
- Customer dashboards
- WooCommerce stores
WordPress Security Headers Checklist
1. Strict-Transport-Security
HSTS tells browsers to use HTTPS for future requests.
Check:
- Is HTTPS enabled?
- Is HSTS present?
- Is the max-age appropriate?
- Are subdomains included only when safe?
- Is preload considered only when the site is ready?
Do not add HSTS blindly. If a site has mixed content or subdomain issues, a bad rollout can create problems.
2. Content-Security-Policy
CSP helps control which scripts, styles, frames, images, and other resources can load.
Check:
- Is CSP present?
- Is it report-only or enforced?
- Are unsafe-inline or unsafe-eval used?
- Are third-party scripts required?
- Does WooCommerce checkout still work?
- Do analytics, ads, chat widgets, and payment providers still work?
CSP is powerful but easy to break. Start carefully and test.
3. X-Frame-Options or Frame-Ancestors
Frame protections help reduce clickjacking risk.
Check:
- Is
X-Frame-Optionspresent? - Is CSP
frame-ancestorsused? - Are there legitimate iframe requirements?
- Are payment or embedded workflows affected?
4. X-Content-Type-Options
This header can help prevent MIME sniffing.
Recommended value:
nosniff
5. Referrer-Policy
Referrer-Policy controls how much URL information is sent to other sites when users click links.
Review:
- Is the policy present?
- Does it reduce unnecessary leakage?
- Does it preserve needed analytics?
Common balanced option:
strict-origin-when-cross-origin
6. Permissions-Policy
Permissions-Policy controls access to browser features such as camera, microphone, geolocation, and payment-related capabilities.
Review:
- Which features does the site need?
- Are unnecessary features disabled?
- Do checkout or embedded tools require anything special?
7. Cross-Origin Headers
Some advanced sites may need cross-origin policies. These should be reviewed carefully because they can affect embeds, scripts, and application behavior.
Security Headers Are Not Enough
Headers are important, but they do not fix:
- Vulnerable plugins
- Weak admin passwords
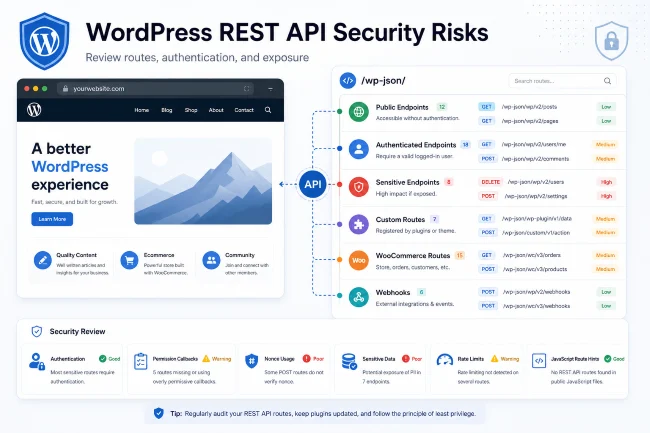
- Exposed REST routes
- Broken access control
- Malware
- Unsafe custom code
- Outdated themes
- Bad file permissions
- Misconfigured webhooks
- Leaked debug logs
That is why Aegisify Audit treats headers as one part of a broader WordPress security audit.
How Aegisify Audit Helps
Aegisify Audit helps review:
- Security headers
- HTTPS/TLS signals
- Public exposure
- Login surface
- REST/API exposure
- Install artifacts
- Debug log exposure
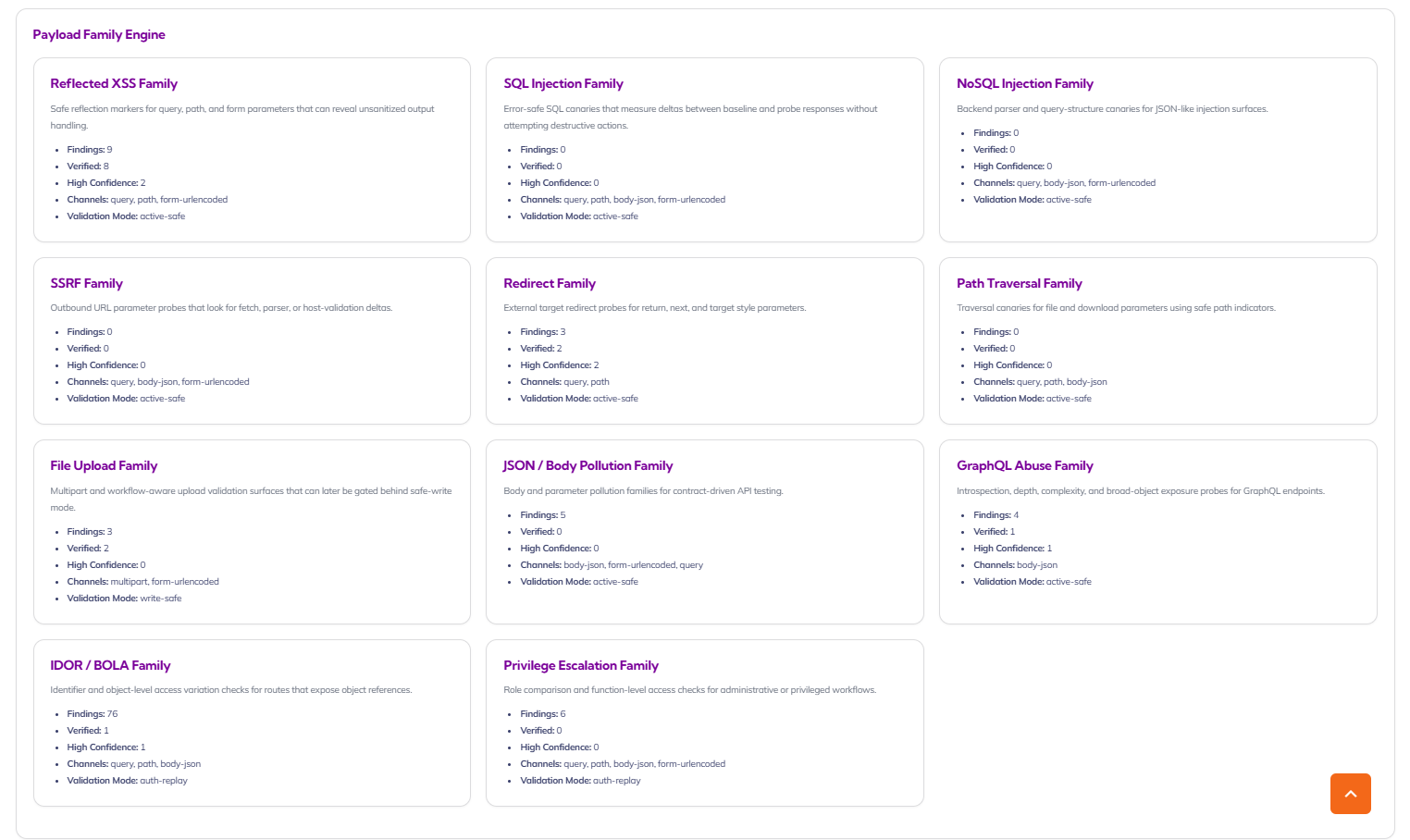
- DAST-style findings
- Vulnerability scan context
- Reports and remediation priorities
This gives site owners a better path than simply adding random headers from a blog post.
Implementation Tips
- Test headers in staging first
- Roll out CSP in report-only mode when needed
- Verify WooCommerce checkout
- Verify payment gateways
- Verify analytics and tag managers
- Verify embedded videos/maps/chat tools
- Retest after deployment
- Include header review in recurring audits
FAQ
Do security headers make WordPress secure?
No. They help reduce certain browser-facing risks, but they are only one layer.
Should every site use the same CSP?
No. CSP should match the site’s scripts, styles, integrations, and business workflows.
Can Aegisify Audit detect missing headers?
Aegisify Audit’s scan workflows include header review as part of public exposure and DAST-style checks.
Start With a Clear Security Picture
Use Aegisify Audit to turn WordPress scan data, logs, vulnerability findings, DAST-style evidence, risk score, alerts, and remediation planning into one professional workflow.
Try Aegisify Audit today!

Why security scan data becomes noisy so quickly
Every serious security expert knows the problem. A full audit can surface:
- configuration weaknesses
- exposed paths and endpoints
- risky behaviors
- repeated findings across similar routes
- medium and high severity items mixed with informational noise
- findings that sound technical but lack business context
Even when the scan engine is doing its job well, the output can still overwhelm the person reading it. That is not because the data is bad. It is because the data is dense.
 WordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access Gallery
WordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access GalleryWordPress API Shield Protection: WordPress API, DDOS, BOT Control, Detailed Logs and Attack Story for Application Security with Web Firewall Access
 WordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth Gallery
WordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth GalleryWordPress Short Links, Smart Linking, SEO, Word Cloud, Bulk Linking, WooCommerce, Analytics & Link Tracking : The Executive Guide to Modern WordPress Growth
 2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud Gallery
2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud Gallery2026 #1 WordPress SEO: AI SEO + Google Search Console (GSC Overview, GSC Schema Intelligence & GSC Search Stats) : Easy to Deploy, Advanced Intelligence Powered by Google Cloud
 2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified Gallery
2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified Gallery2026 #1 WordPress Security Application : WordPress Security, Application Security, Web Application Hardening, Login Guard & File Integrity Unified