WordPress Critical Files Monitoring: Protect wp-config.php, Core Files, and File Integrity with Aegisify Shield
Most WordPress security conversations focus on malware scans, login protection, plugin vulnerabilities, and firewall rules. Those matter. But there is another layer that deserves serious attention: WordPress critical files.
Files like wp-config.php, .htaccess, wp-login.php, wp-settings.php, and other WordPress bootstrap files play a major role in how a site loads, connects, authenticates, and behaves. When one of these files changes unexpectedly, site owners need more than a generic “file changed” message. They need context, visibility, and a clear review path.
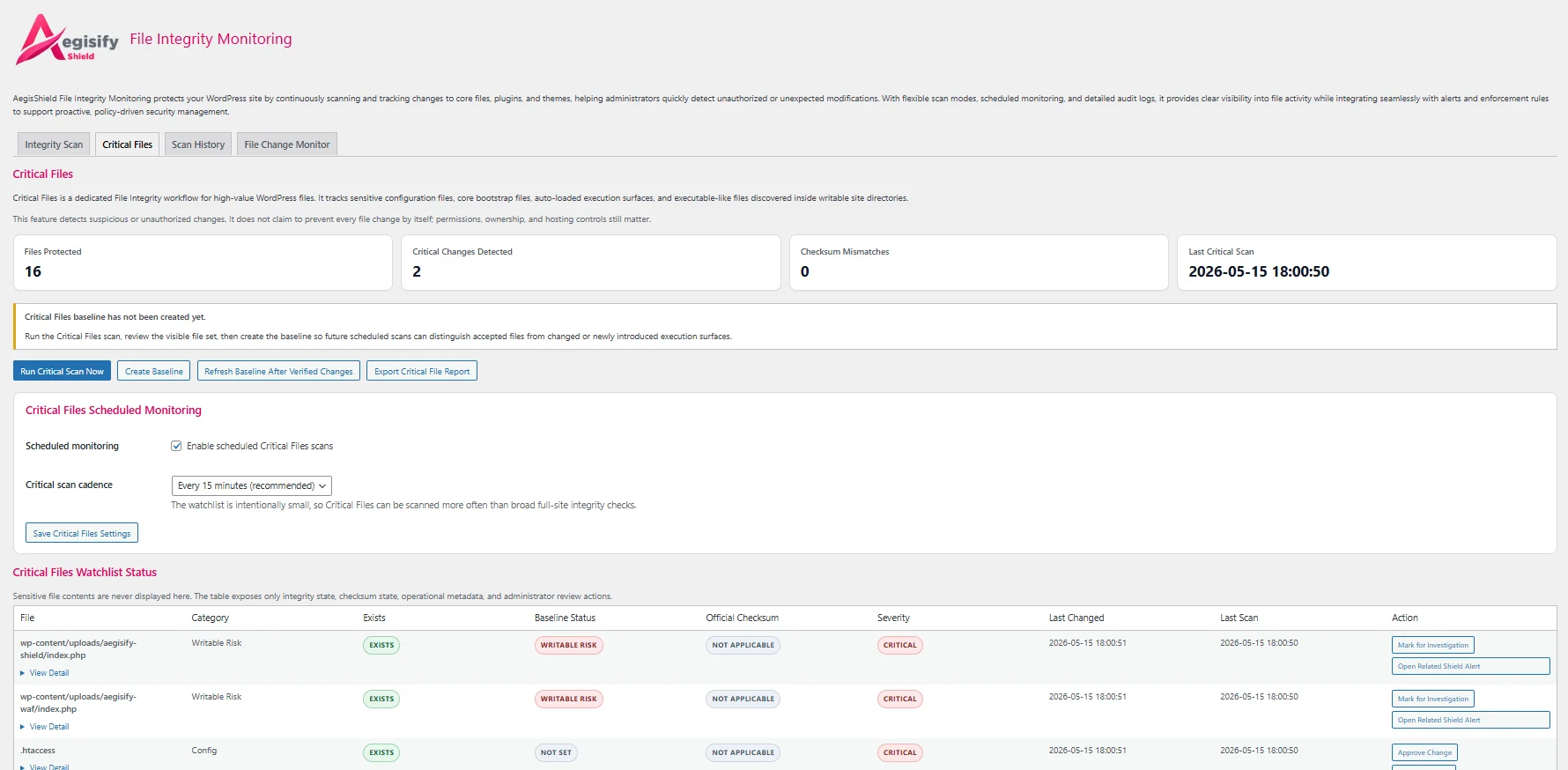
That is why Aegisify Shield now includes Critical Files, a dedicated WordPress file integrity monitoring workflow built to watch the high-value files that deserve faster attention.
Why WordPress Critical Files Matter
WordPress identifies wp-config.php as one of the most important files in a WordPress installation because it stores the site’s core configuration details, including database connection settings. WordPress hardening guidance also treats sensitive configuration and file-access controls as a key part of site security.
A changed critical file is not always malicious. A security plugin, cache plugin, host adjustment, or administrator action may legitimately update a file. But an unexpected change can also point to:
- Unauthorized edits
- Malware injection
- Unexpected redirects
- Modified login or bootstrapping behavior
- Changes that weaken security posture
The problem is not simply that files change. The problem is knowing which changed files matter most, what changed, and what should be reviewed first.
What Aegisify Shield Critical Files Monitors
Aegisify Shield Critical Files creates a separate, focused monitoring layer for high-value WordPress files. Instead of treating every file change the same, it watches a defined set of files and execution surfaces that deserve elevated attention.
1. Critical Configuration Files
- wp-config.php
- Parent-directory wp-config.php, when used
- .htaccess
- web.config, when present
These files can influence configuration, rewrite rules, access behavior, and critical site operations. Aegisify Shield keeps them in a dedicated WordPress critical file protection workflow instead of letting them blend into a large general-purpose scan.
2. WordPress Core Bootstrap and Entry Files
- index.php
- wp-load.php
- wp-settings.php
- wp-blog-header.php
- wp-login.php
- wp-cron.php
- xmlrpc.php
- wp-comments-post.php
These are core WordPress files that normally should not be casually edited. Aegisify Shield checks these files using a combination of live file hashing and WordPress checksum verification, helping identify unexpected or suspicious changes to important WordPress core components.
3. Auto-Loaded Execution Surfaces
- MU plugins
- advanced-cache.php
- object-cache.php
- db.php
- sunrise.php, where applicable
These files can execute early in the WordPress lifecycle or load automatically. That makes them important to monitor, especially on sites where administrators want stronger visibility into hidden or less frequently reviewed execution points.
4. Suspicious Executable Files in Writable Directories
Critical Files also surfaces executable-like files discovered in writable locations such as:
- Uploads directories
- Cache folders
- Backup or export folders
- Temporary folders
This helps flag risky file placements such as unexpected .php, .phtml, .phar, or double-extension files in places where they deserve review.
How Aegisify Shield Critical Files Works
Step 1: Create a Trusted Baseline
The workflow begins by creating a baseline for monitored files. Aegisify Shield records the accepted state of the file and now also stores a protected baseline snapshot, giving the administrator a better point of comparison later.
Step 2: Monitor for Changes
Critical Files scans can run manually or on a scheduled cadence. The system checks watched files for:
- Changed hashes
- Missing files
- New files where they deserve review
- Official checksum mismatches for supported WordPress core files
Step 3: Alert When Something Needs Attention
When a critical file changes unexpectedly, Aegisify Shield can generate a WordPress file change alert with enough detail to help the administrator decide what to review next. This includes the file involved, the security context, and a direct route back to the Critical Files area for investigation.
Step 4: Review the Diff
Aegisify Shield adds a Diff view that compares the saved baseline file snapshot against the current live file. Instead of simply seeing that a file changed, administrators can review what changed.
For sensitive files like wp-config.php, protected values are redacted in the diff so the review process adds clarity without exposing secrets.
Step 5: Approve or Investigate
If a change is known and expected, an administrator can approve it and refresh the baseline. If it is unclear or suspicious, it can be marked for investigation. This creates a cleaner review flow than simply generating alerts with no next step.
The Benefits of WordPress Critical Files Monitoring
Faster visibility into high-risk file changes
A dedicated WordPress critical files view helps site owners focus on changes that deserve priority, rather than getting lost in broad file-change noise.
Better review of wp-config.php and core file changes
Because wp-config.php monitoring is handled directly, administrators gain clearer oversight into one of the most important files in WordPress.
Official checksum awareness for core integrity
Aegisify Shield compares supported WordPress core files against official checksum data, adding stronger context to WordPress core file integrity reviews.
Baseline snapshots and file diff review
The new baseline snapshot and diff workflow help answer a practical question: what changed inside the file? That makes the feature useful for real-world security triage and controlled administrator review.
Cleaner decision-making for site owners, agencies, and operators
Aegisify Shield Critical Files is especially useful for:
- WordPress site owners managing business-critical websites
- Agencies overseeing many client sites
- WooCommerce operators protecting revenue workflows
- Teams that want stronger visibility into file-level WordPress changes
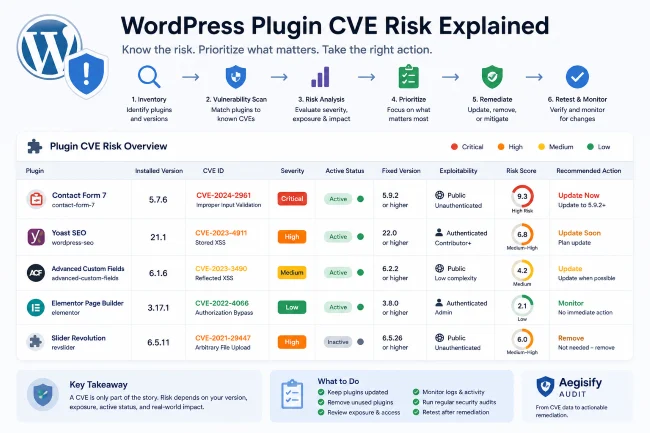
How Aegisify Shield Critical Files Compares with Other WordPress Security Tools
| Tool | Publicly Documented File Integrity Focus | Where Aegisify Shield Critical Files Stands Out |
|---|---|---|
| Wordfence | Scans files, recognizes known-good core/theme/plugin files, and deeply scans unrecognized files for suspicious patterns. | Aegisify Shield adds a dedicated Critical Files workflow centered on high-priority WordPress files, baseline snapshots, and direct diff review. |
| Sucuri | Documents WordPress core integrity checks powered by official checksum data. | Aegisify Shield extends the workflow into site-specific sensitive files such as wp-config.php, .htaccess, drop-ins, MU plugins, and writable-folder executable review. |
| Solid Security | Provides file-change monitoring and file-change alerts in its security dashboard workflow. | Aegisify Shield positions the new feature around high-value critical file monitoring, file-specific baselines, alerts, and diff-assisted review. |
Based on current public documentation, the competitor landscape already confirms that file integrity and file-change detection matter. Aegisify Shield’s opportunity is to make the experience more focused around WordPress critical files and more actionable when those files change.
Why This Matters for Serious WordPress Sites
A modified file does not automatically mean a site is compromised. But on a serious WordPress site, certain files deserve faster review than others. A business should not treat a changed thumbnail cache file the same way it treats a changed wp-config.php file.
That is the real value of Aegisify Shield Critical Files:
- It highlights the files that deserve priority.
- It adds context around file integrity.
- It helps administrators review what changed.
- It turns a raw file alert into a more useful security workflow.